Threat Response - Integrating with an Abuse Mailbox¶
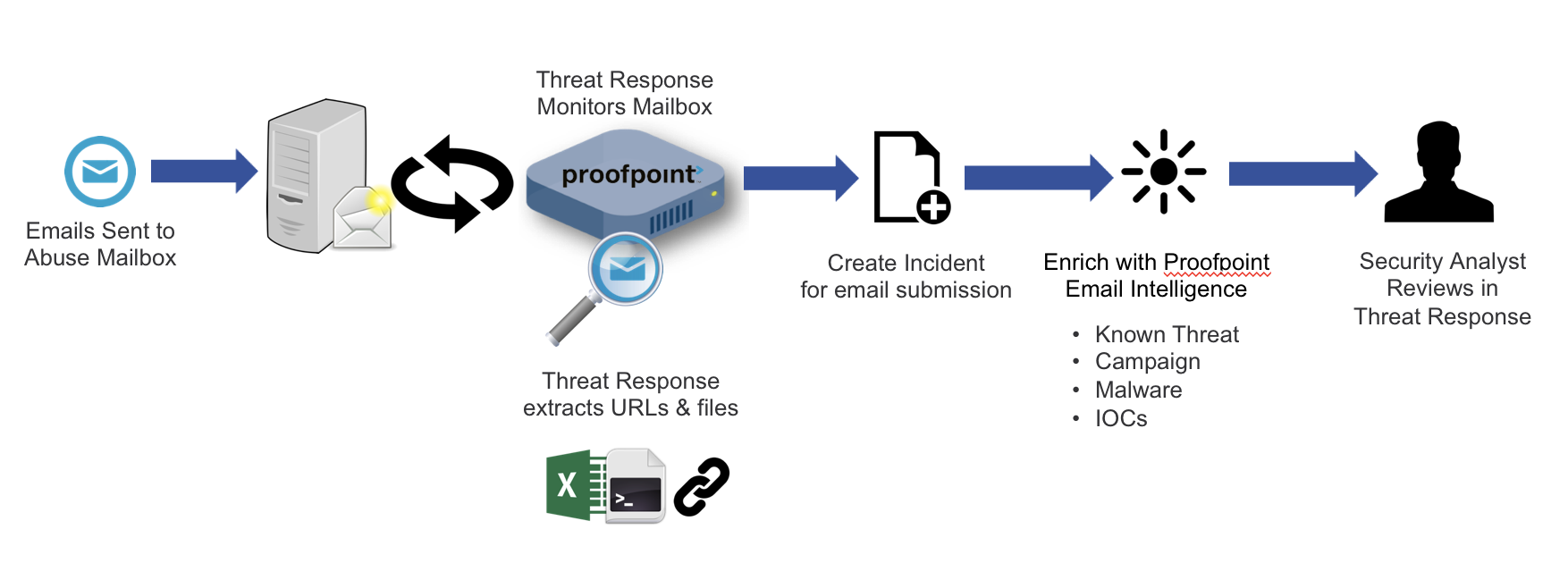
Threat Response 3.5 introduced the ability to manage Abuse Mailboxes. This allows security analysts to use Threat Response to monitor an abuse mailbox to quickly understand the context around user-reported potentially malicious emails. Abuse mailboxes on MS Exchange, Office 365 and Gmail are supported.
This event source is available to Threat Response Auto Pull (TR-AP) licensed customers.
Feature Overview¶
Support for multiple mailboxes and folders
Each mailbox and folder combination can be configured as an independent “Abuse Mailbox” Source.
Incident Creation
For each message that is found in an abuse mailbox, PTR will automatically generate at least one alert, and create an incident or link to an existing incident (linked via the message-ID of the original message).
If the original message can be found in the reporter’s mailbox, a separate alert will be generated for each recipient found in the To:, CC: and BCC: fields - these alerts will all be linked to a single incident. If the original message can’t be found, a single alert will be generated based on the reporter’s email address.
Automatic Enrichment
For each alert generated, PTR will enrich with Proofpoint’s email threat intelligence including information such as campaign, URL and file hash reputation.
PTR will also break down the message and display the body content and message headers.
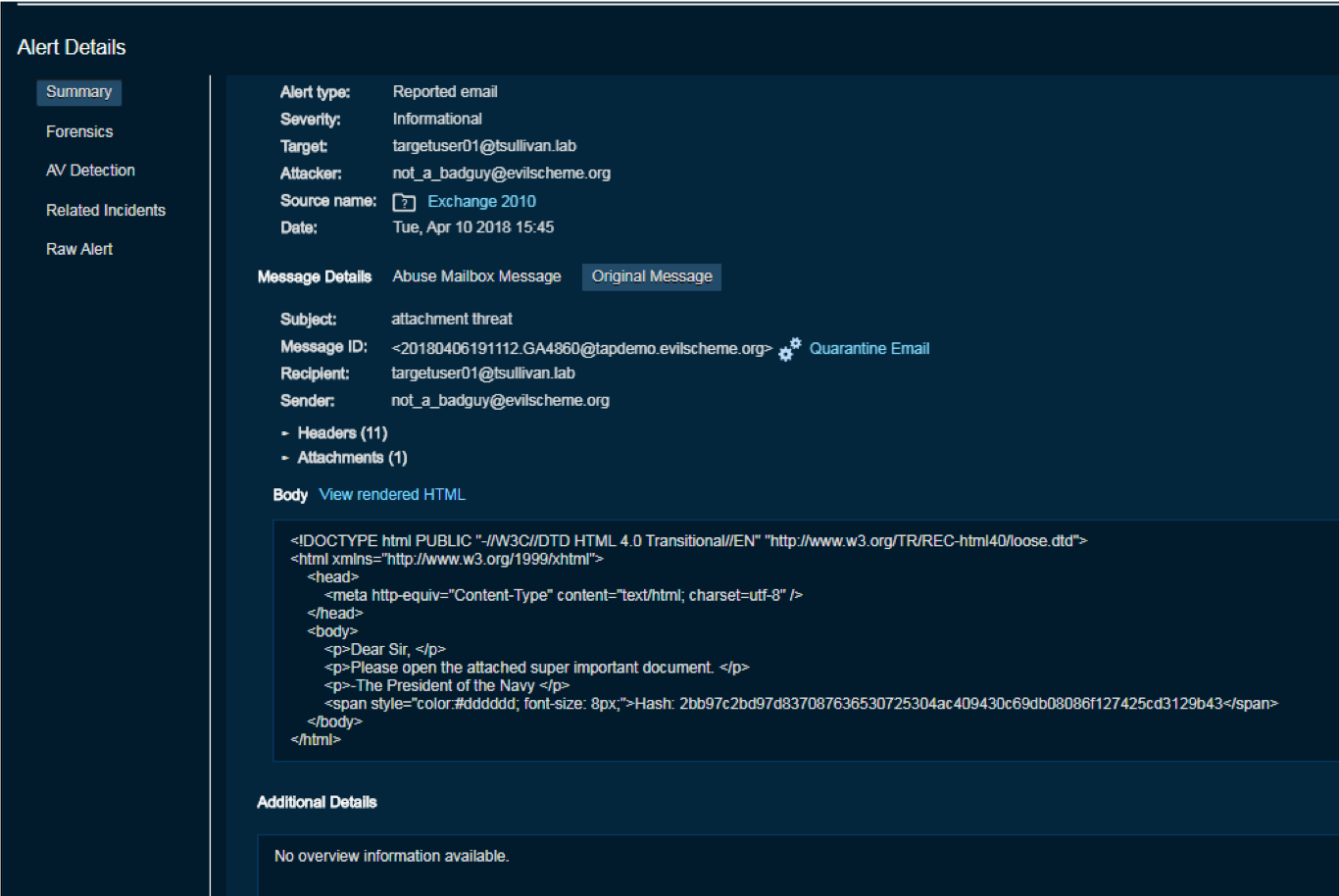
Email Quarantine
If an analyst determines the user-submitted message to be malicious, they can trigger a manual quarantine of the original message as long as PTR can find the original message in the reporter’s mailbox, or if the original message was submitted to the abuse mailbox as an attachment (Exchange only). The quarantine response will follow the same process as quarantining from any other source, including forward following and distribution list expansion.
Note
Introduced in version 4.2.0 is the ability to create match conditions to automate the quarantine response.
A new option to “Close email-related incidents” has been added to the “Move email to quarantine” response action. If enabled, a successful quarantine of an email from an alert will result in any other alerts referencing the same recipient/message ID pairing will be closed automatically. This is useful to help close user-reported incidents from the Abuse Mailbox where Threat Response has already quarantined the message based on a TAP alert.
Enhanced Integration with PhishAlarm Analyzer¶
There are additional integration benefits for customers who have also purchased Proofpoint’s PhishAlarm and PhishAlarm Analyzer:
Enhanced severity settings for Abuse incidents where the source of the reported email is PhishAlarm Analyzer
- Incidents will be assigned the following severities in Threat Response based on PhishAlarm Analyzer’s confidence in the email being a Phish:
- Unlikely a phish: Informational
- Suspicious: Minor
- Likely a phish: Major/High
Note
For more info on this integration, please see the Proofpoint Clear integration guide.
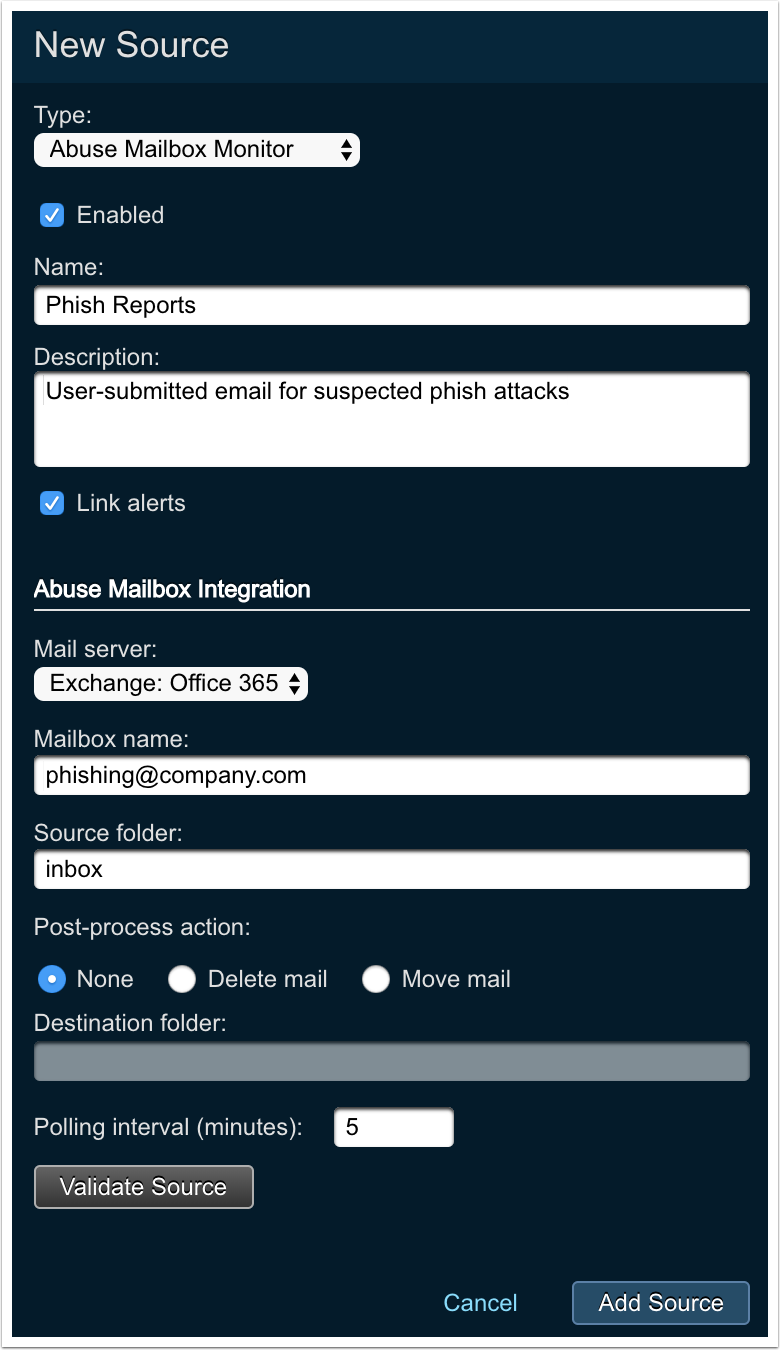
Configuring an Abuse Mailbox Event Source¶
The steps below describe the process of creating an Abuse Mailbox event source in Threat Response.
Tip
Multiple abuse mailboxes can be configured within Threat Response and can monitor mailboxes in different mail environments. Ensure the email servers have been created in System Settings > Email Integration prior to following the steps below.
For each mailbox you wish to monitor, you need to create an event source in Threat Response.
- Log in to Threat Response.
- Navigate to the
Sourcespage. - Click on the plus sign next to Sources to create a
New Sourcepanel. -
Set the following fields:
- Type: Abuse Mailbox Monitor.
- Name: provide the name of the event source.
- Description: provide the description of the event source.
- Link events: “Enable” to give Threat Response permission to group alerts into incidents automatically.
- Mail Server: this server resides with the abuse mailbox (pulled from the list of Exchange/O365/Gmail servers configured in
System Settings). - Mailbox Name: the SMTP address of the abuse mailbox.
- Source Folder: the folder within the abuse mailbox to be monitored.
- Post-Process Action: the action to be taken after PTR processes a message and creates an incident.
- None: the message read from the abuse mailbox is untouched and remains in the mailbox.
- Delete the Message: after reading the reported abuse message and creating an alert, the abuse message in the abuse mailbox is deleted.
- Move the Message: after reading the reported abuse message and creating an alert, the abuse message is moved to the specified folder.
- Destination Folder: if the post-process action is “Move mail,” then this is the folder to which the message is moved.
- Polling Interval: the time, in minutes, that Threat Response waits to check for new messages in the mailbox. Permitted values: one to sixty minutes.
- Click on
Add Source.