Threat Response - Integration With Carbon Black EDR¶
Threat Response supports integeration with Carbon Black. The following functionality is supported today:
- Manually isolate a host using Carbon Black
- Use Carbon Black EDR for IOC (Indicator Of Compromise) collection as an alternative to the native Proofpoint Threat Response PC Data Collection agent.
Support for Carbon Black EDR as IOC collector
Supported Carbon Black Versions
Threat Response supports Carbon Black server versions 5.x and 6.x for peforming IOC collection.
IOC Items collected
Using the Carbon Black server APIs, Threat Response collects the following IOC data:
-
File system changes
-
Network activity
-
Processes
-
Registry changes
Infection Analysis
Threat Response uses the IOCs collected from Carbon Black to identify any IOCs that match forensics event data resulting in an IOC Confidence score
Threat Response configuration¶
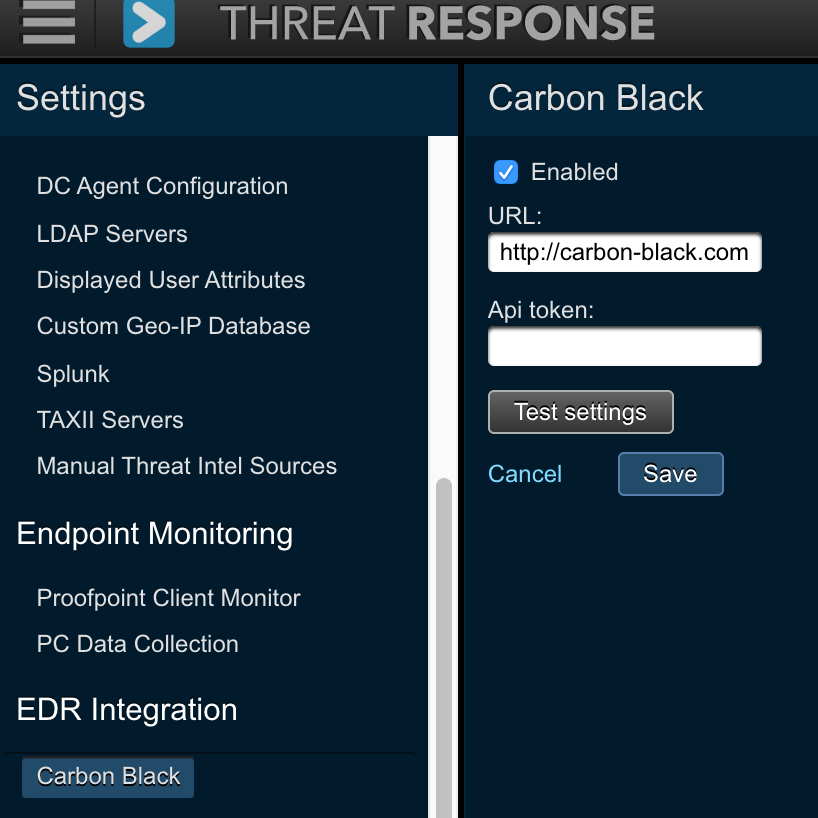
To configure host isolation with Carbon Black, a Threat Response admin user needs to perform the following steps:
- Log in to Threat Response
- Go to
System Settings>Carbon Black - Define the following parameters
- URL: URL to reach Carbon Black
- API token: API token to use with every API request
- Check
Enabled - Test integration using
Test settingsbutton - Click
Save
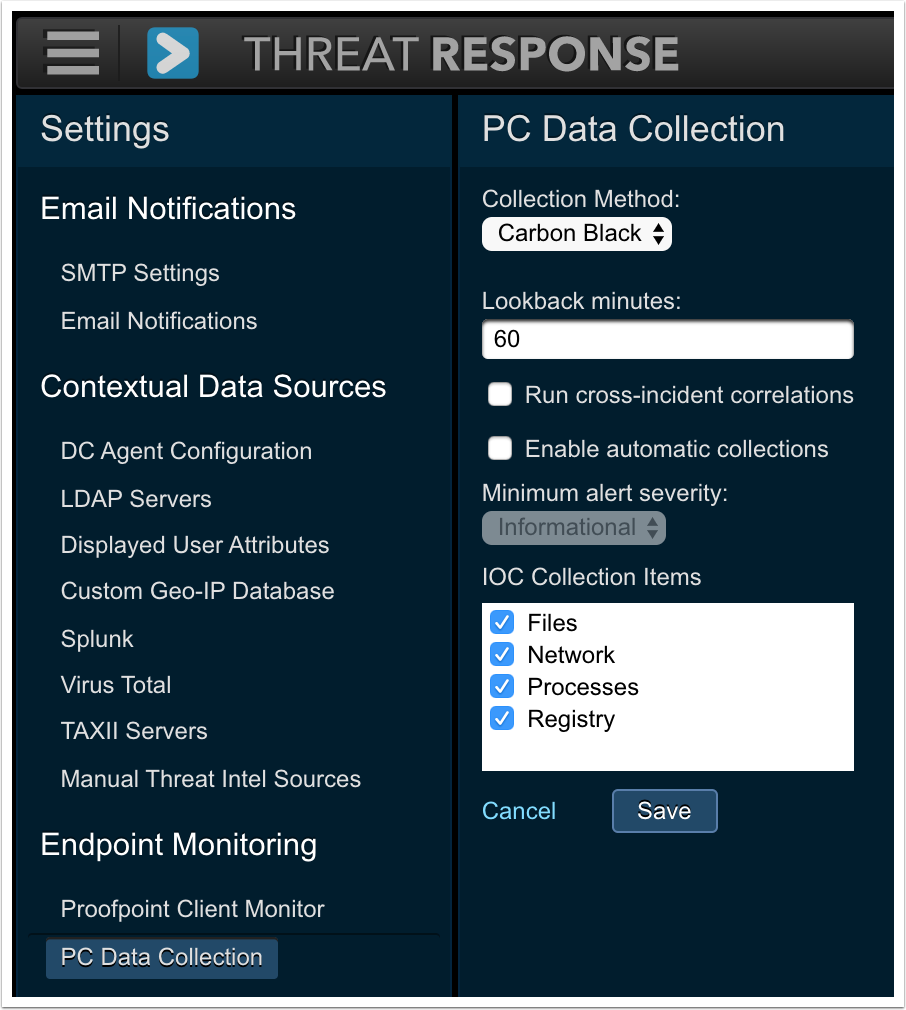
To configure Threat Response to use Carbon Black for IOC collection, first follow the instructions above to enable host isolation, then follow the steps below:
- Log in to Threat Response
- Go to
System Settings>PC Data Collection - Change the Collection Method from “Collector” to “Carbon Black”
- Define the desired Lookback Minutes (used when collecting File & Registry changes)
- Optionally enable cross-incident correlations and/or automatic collections
- Choose which IOCs to collect
- Click
Save