Proofpoint CSV Upload
Threat Response version 3.5 introduced the ability to ingest a generic list of alerts from a file in comma-separated values format. This file is ingested to an event source within the Threat Response platform and will create an individual event for each row in the file. The process of uploading the file is currently manual, however, as with all event sources within Threat Response, it is possible to create a Match Condition that can take automated actions.
This event source is available to Threat Response Auto Pull (TR-AP) licensed customers.
Configuring the CSV Upload Source¶
This section will cover the steps for configuring a CSV Upload alert source. It is important to note that only one instance of this alert source is able to be configured per Threat Response Instance.
Navigate to the Alert Sources Configuration Page¶
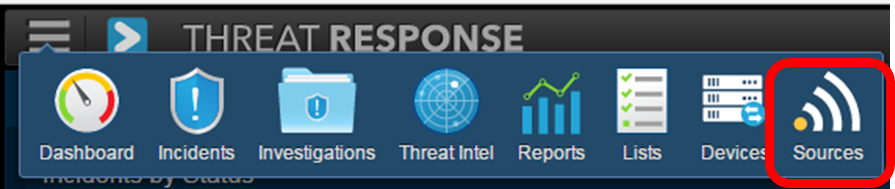
- Log into Threat Response with an administrator level account
-
Using the navigation drop down menu, navigate to the ‘Sources’ page
Create a New CSV Upload Alert Source¶
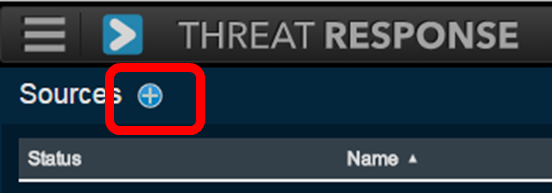
-
Click the plus symbol to the right of Sources to add a new source:
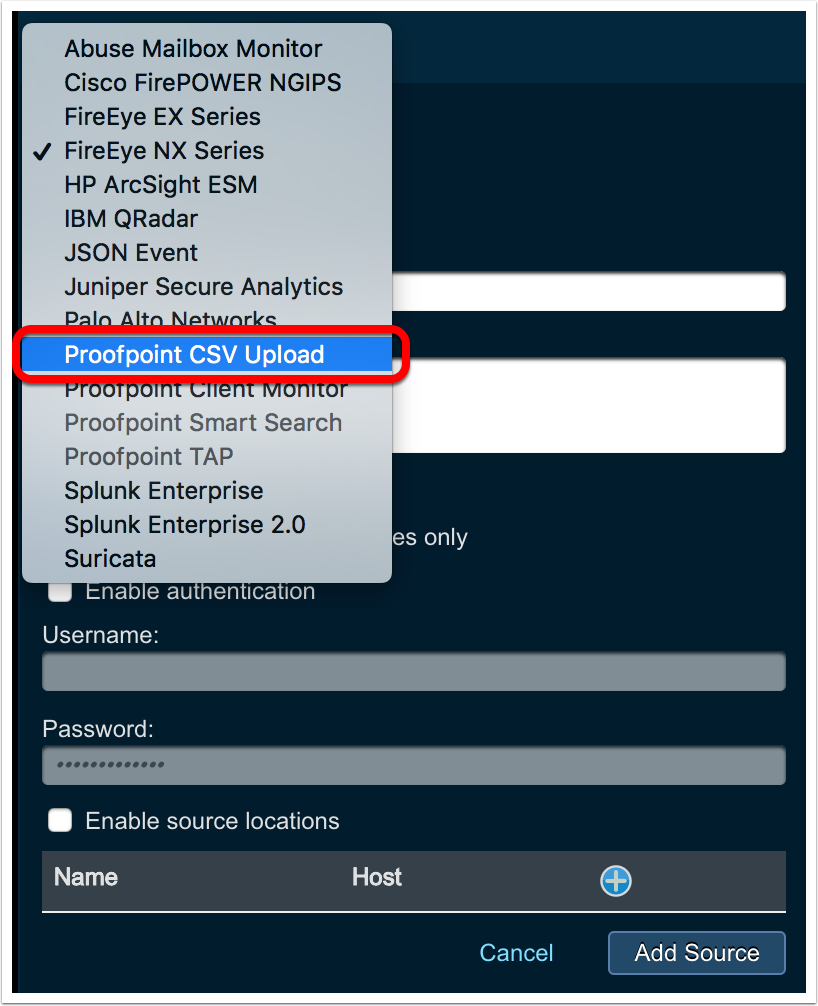
-
In the right hand pane select “Proofpoint CSV Upload” from the drop down menu under ‘Type’
-
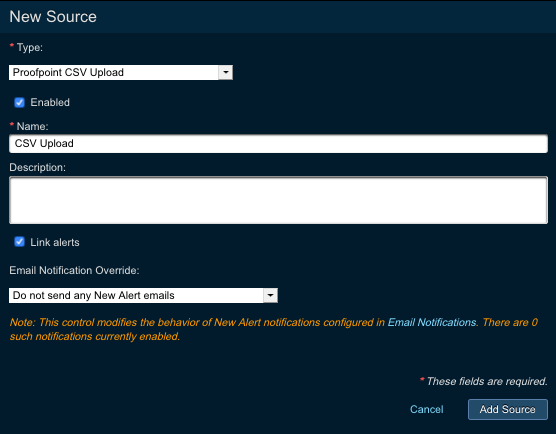
Within the ‘New Source’ window configure the following:
‘Enabled’ checkbox: Clearing the checkbox will disable the event source while selecting the box will enable it.
Name (Required Field): Provide a name for the event source. This is an internal name only and can be whatever is most helpful to the administrator or operators.
Description (Optional Field): Provide any desired description of the event source
‘Link Alerts’ checkbox: Clearing the checkbox will result in an individual incident being created per alert (1 to 1). Selecting the checkbox will leverage Threat Responses linking logic to group similar alerts into relatable incidents.
-
Once the proper information has been configured select ‘Add Source’ in the lower right corner.
-
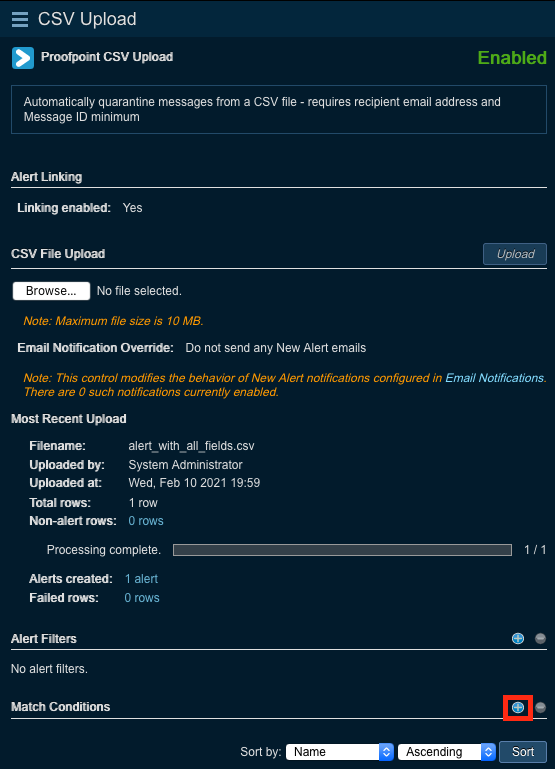
Validate that the desired configuration has been saved to the new source
Configuring Match Conditions¶
This section will cover the steps for creating, modifying and removing Match Conditions.
Creating Match Conditions¶
A Match Condition is a configuration that allows Threat Response to take automated action based on certain criteria found in the reviewed alert.
-
To create a new Match Condition select the ‘plus’ symbol to the right of ‘Match Condition’
-
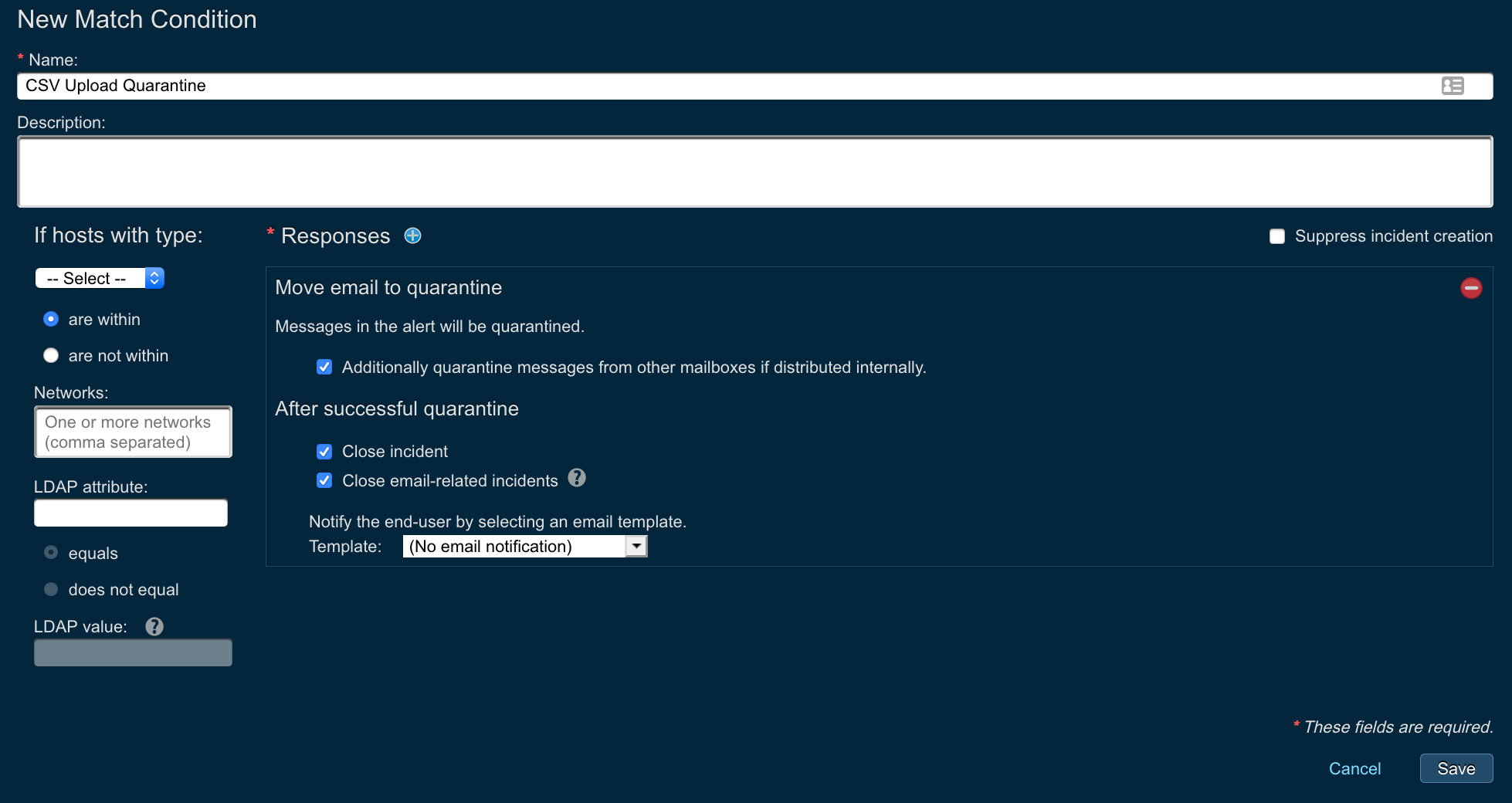
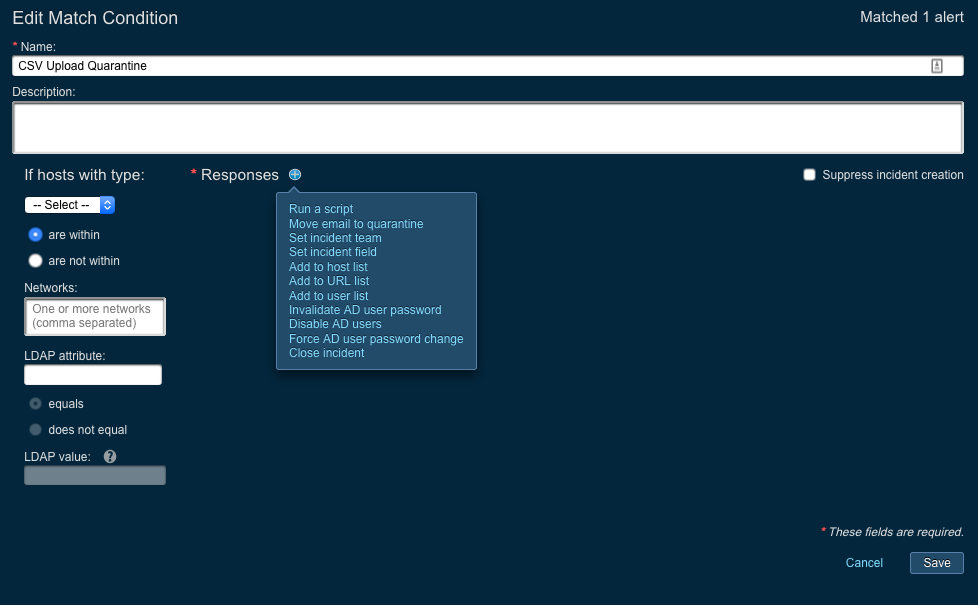
Within the ‘New Match Condition’ configure the following:
Name (Required Field): Provide a name for the event source. This is an internal name only and can be whatever is most helpful to the administrator or operators.
Description (Optional Field): Provide any desired description of the event source
If hosts with type (optional): Select the host type to be specified in the dropdown menu
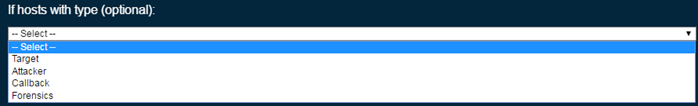
Target: The host/IP address (es) that are indicated as the target of the attack
Attacker: The host/IP address(es) are indicated as the source of the attack
Callback: The host/IP address(es) that suspected malware is seen attempting to contact
Forensics: The host/IP address(es) that are seen within a sandbox detonation that do not fall into the previous categories.
Are within | are not within: Radio button selections to specify if the hosts type selected is of is not within certain networks or IP ranges
Networks: Use to specify the network information for the previous step. It is required when ‘If hosts with type’ has been selected.
LDAP Attribute (optional): Provides a dropdown list/text box to enter in an LDAP attribute. In order for the alert to match on an LDAP attribute Threat Response must be configured to retrieve that attribute. To configure this collection please refer to the admin guide. The dropdown list will only populate with attributes collected.
LDAP value: This test field is grey out unless the LDAP attribute field is configured. It is required to be populated when active.
Suppress incident creation: A checkbox that can be select so that the match condition will take the appropriate action but will not create an incident for the alerts that have been matched nor retain the alert information..
Responses (Required Field): The response action to take when the match condition criteria is met. The available responses are dynamic and will only appear if certain configurations have been made. For example if no lists have been configured then the options ‘Add to host list’, ‘Add to URL list’, ‘Add to file list’ and ‘Add to user list’ will not be available.
Save: After reviewing the settings, select save to save and apply the filter.
Changing Match Conditions¶
-
Select the appropriate Alert Source
-
In the right hand pane identify the Match Condition to change
-
Click ‘Edit’ in the bottom right corner of the Match Condition
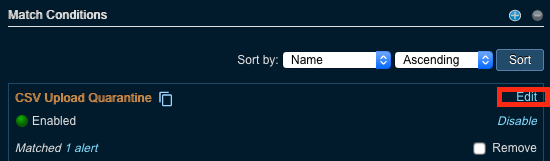
-
Make appropriate adjustments and save the Match Condition. Reference “Creating Match Conditions” in this document for specifics about each configurable setting.
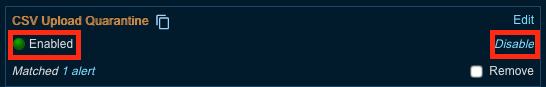
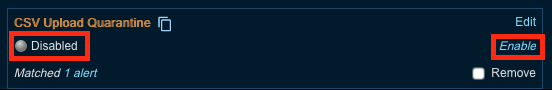
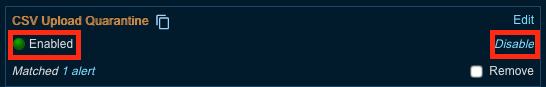
Disabling Match Conditions¶
You can easily see if a match condition is enabled or disabled by looking at the “Enabled” text with a green icon or “Disabled” text with a grey icon on the left hand side of the match condition.
To disable/enable a match condition:
-
Select the appropriate Alert Source
-
In the right hand pane identify the Match Condition to disable
-
Click ‘Disable’ in the bottom right corner of the Match Condition
-
The selection in the bottom right corner should change to ‘Enable’ and the text on the left side should show “Disabled” with a grey circle.
-
Select the appropriate Alert Source
-
In the right hand pane identify the Match Condition to enable
-
Click ‘Enable’ in the bottom right corner of the Match Condition
-
The selection in the bottom right corner should change to ‘Disable’ and the text on the left side should show “Enabled” with a green circle.
Remove Match Conditions¶
-
Select the appropriate Alert Source
-
In the right hand pane identify the Match Condition to remove
-
Click checkbox on the right of the Match Condition to remove
-
Click the red circle indicator that becomes active opposite the ‘Match Condition’ heading
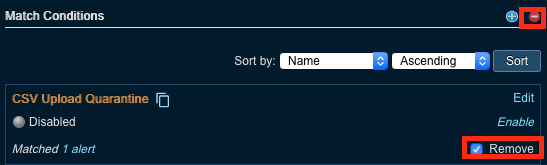
NOTE There is no warning given to verify and there is no way to undo this action.
Creating and Uploading a CSV File¶
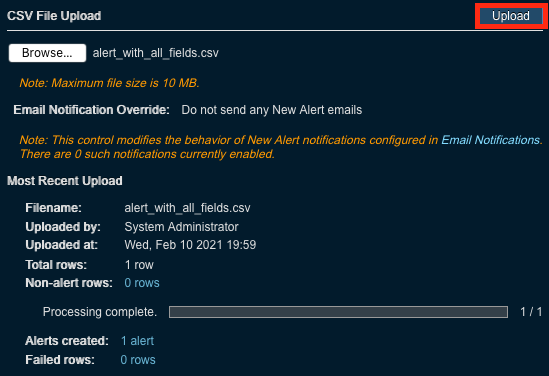
This section will cover the steps for creating and uploading the CSV file. The CSV file must be less than 10MB in size and contain less than 10,000 rows; any attempts to upload a larger CSV file will result in an error message being shown.
Creating the CSV Upload File¶
The CSV file must contain a header row, and to enable email quarantine, must contain at a minimum the message ID and recipient’s email address.
Note
The field names are case-sensitive. For proper field mapping, please ensure you use the correct case.
Some commonly used fields:
- Classification (e.g. malware, phish)
- Description
- Severity (Critical, High, Medium, Low, Informational)
- Message ID (required for email quarantine)
- Email Sender
- Email Subject
- Email Recipient (required for email quarantine)
- Email Delivery Time
See this sample file for the complete list of available fields.
Note
You can upload a CSV file with just the two required columns - Message ID and Email Recipient, for executing email quarantine responses. The other columns can be optionally filled in to populate the corresponding alert fields in Threat Response.
Uploading the CSV to Threat Response¶
-
Navigate to the ‘Sources’ page
-
Select the appropriate ‘CSV Upload’ alert source
-
Ensure that the alert source is enabled
Optional: Ensure that any match conditions are properly configured and enabled prior to continuing to take automated action.
-
Under ‘CSV Upload CSV File’ click ‘Choose File’ to locate the CSV export
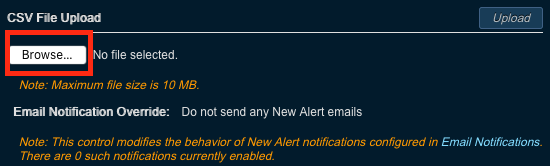
-
Select the appropriate file and click ‘Open’
-
Ensure that the correct file name is displayed next to the ‘Choose File’ button
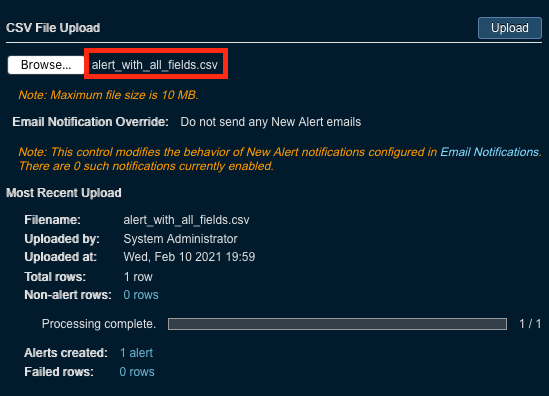
-
Select ‘Upload’ to upload the alerts into Threat Response
-
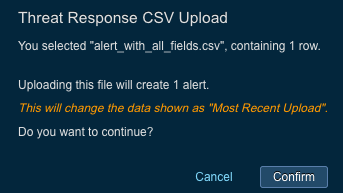
A popup window will appear detailing the number of rows that the file contains as well as the number of alerts that will be created. Validate the information and click Confirm.
-
The file will now be converted to alerts within Threat Response.
Best Practice Match Condition¶
There is one recommended match condition for the CSV Upload source as part of Threat Response best practices. This match condition simply quarantines the emails listed in the uploaded CSV file.