Threat Response - Integration with FirePower¶
The Cisco FirePOWER platform is the underlying framework for Cisco’s threat detection services that include both next-generation IPS (NGIPS), and malware detection. The FirePOWER platform can generate IDS/IPS alerts to Threat Response for incident management and containment as threats are detected on the network.
This document details the configuration process to send Cisco FirePOWER NGIPS alerts to Proofpoint Threat Response.
Supported Cisco FirePOWER versions include:
| Platform | Version |
|---|---|
| Cisco FirePOWER NGIPS | Supported: Sensor: 6.0, Management Center: 5.4.0 |
Forwarding Alerts to Threat Response¶
Cisco FirePOWER can forward alerts to Threat Response so that they can be managed using Threat Response’s incident response workflow. This chapter will detail the process of both configuring an alert listener in Threat Response, as well as configuring FirePOWER to forward alerts to Threat Response via syslog.
Creating an Alert Source in Threat Response¶
You must first create an event source in Threat Response to receive alerts from the Cisco FirePOWER system. The steps below outline the source creation process.
To create a Cisco FirePOWER alert source:
- Log in to Threat Response.
- Navigate to the
Sourcespage. - Click the blue
Add (+)button next toSourcesto bring up theNew Sourcepanel. - Set the following fields:
- Type:
Cisco FirePOWER NGIPS - Name:
<alert_source_name> - Description:
<description> - Link Events:
<checked>
- Type:
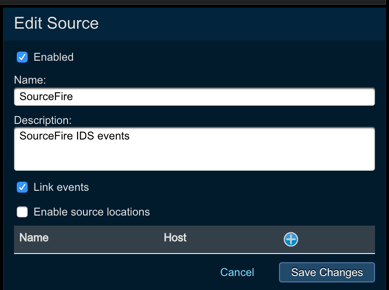
Savechanges.
With the source configured, Threat Response is now ready to receive alerts from Cisco FirePOWER. The remainder of the configuration lies in FirePOWER.
Note
Due to the syslog nature of these alerts, Threat Response only allows the creation of a single Cisco FirePOWER NGIPS event source.
Configuring Alert Forwarding in Cisco FirePOWER¶
With the alert source created in Threat Response, you can now begin sending FirePOWER alerts to Threat Response. To complete the configuration, we will use the Cisco FireSIGHT Management Center to enable, and configure syslog alerting.
To configure syslog alerting using Cisco FireSIGHT Management Center:
- Log in to the Cisco FireSIGHT Management Center.
- Navigate to
Policies>Intrusion>Intrusion Policies.
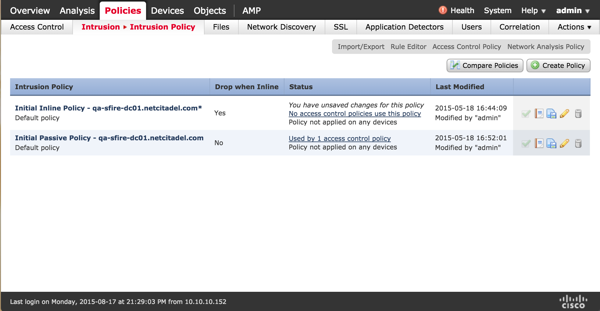
- Click the
Editicon to open the policy that you want to forward to Threat Response. - Once the policy has loaded, click
Advanced Settings. - Enable the
Syslog Alertingfeature, and click theEditicon forSyslog Alertingto display the syslog configuration. - Configure the following syslog settings:
- Logging Hosts:
<threat_response_ip> - Facility:
LOCAL0 - Priority:
NOTICE
- Logging Hosts:
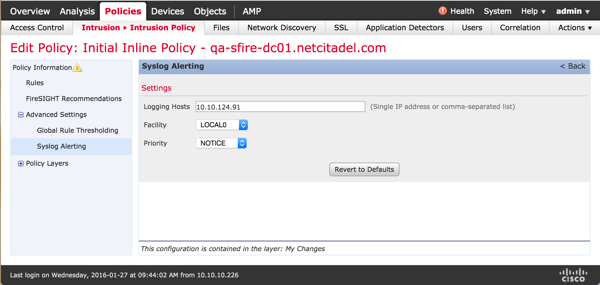
- In the left-hand navigation menu, click Policy Information, and commit your changes.
With the configuration changes in place, Threat Response will begin receiving alerts from the Cisco FirePOWER NGIPS.