Threat Response - IAM and 2FA integration¶
Proofpoint Threat Response will integrate with IAM (Identity Access Management) solutions and 2FA (Two-factor authentication solutions) through Active Directory.
Upon receiving the security event Threat Response can manually or automatically place the user associated with the security event into a pre-determined Active Directory group. When that quarantined user tries to access corporate applications using SSO or login to VPN using 2FA, IAM and 2FA solutions can immediately implement higher security controls around that user’s access rights and capabilities on critical assets.
To facilitate this interaction, a Security Group should be created in Active Directory that can be used within Threat Response as part of the incident response process. When creating your group, ensure that the group’s naming convention fits within your security team’s workflow for identifying users that may pose a security threat.
Synchronizing Threat Response to Active Directory¶
For demonstration purposes here, we will utilize a group called PTR_Suspicious_Users. Any user reported in a security incident will be immediately placed into this group while an investigation commences.
Note
It is recommended to name Security Groups utilized by Threat Response such that they are easily recognizable within your groups list in Active Directory. In our example, we have prefixed the group name with “PTR_” so that we know this is a group managed by Threat Response.
Once the group has been created, you can follow the steps below to link Threat Response to the group. You will first create a local list in Threat Response that analysts can place users into. You will then connect Threat Response to Active Directory, and create a list mapping to map the local list in Threat Response to the group in Active Directory.
Step 1: Create a list in Threat Response¶
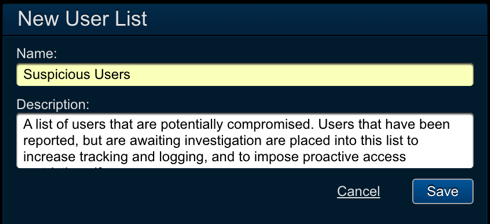
- Log in to Threat Response.
- Navigate to the
Lists>User Listspage. - Click the blue
Add (+)button to create a new user list. - Configured the following fields:
- Name:
Suspicious Users - Description:
<list_description>
- Name:
- Save changes.
Step 2: Create an Active Directory device in Threat Response¶
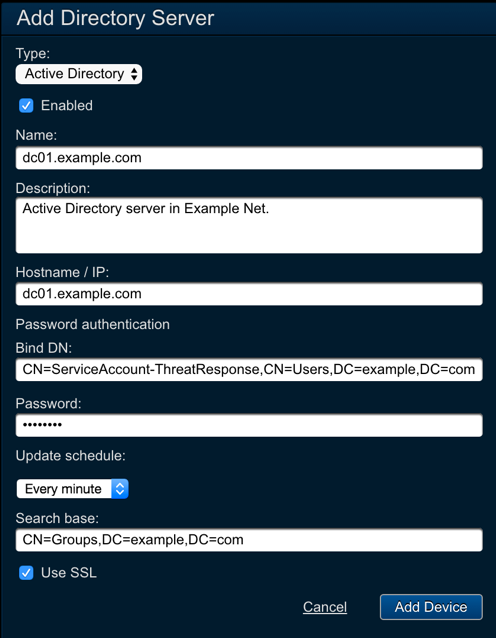
- Navigate to the
Devices>Directory Serverspage. - Click the blue
Add (+)button to connect to a new directory server. - Configured the following fields:
- Type:
Active Directory - Name:
<server_name> - Description:
<description> - Hostname / IP:
<ip_or_hostname> - Bind DN:
<user_dn> - Password:
<password> - Update Schedule:
Every minute. Note: Setting the Update Schedule to Every Minute ensures that any pending updates will be synchronized to this device within 60 seconds. This can be adjusted to comply with your organization’s change policies. - Search Base:
<ldap_search_base>
- Type:
Savechanges.
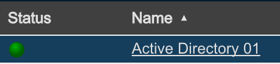
Upon saving the change, you will see your new device appear in the table to the left. Ensure that the status icon changes to a green color prior to moving on.
Step 3: Map the User List to the Security Group¶
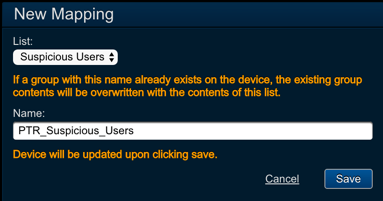
- In the device panel for your new device, locate the
Mappingssection. - Click the blue
Add (+)button to connect to a new list mapping to the device. - Configured the following fields:
- List:
<user_list_name> - Name:
<security_group_name>. Note: Upon clicking Save, Threat Response will connect to the device to ensure that the group exists, and then perform its first sync. Any existing data in the group will be overwritten at this time.
- List:
Savechanges.
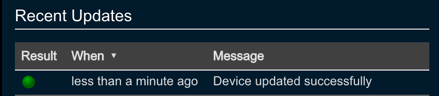
When the mapping is saved, Threat Response will immediately check the server to ensure the Security Group exists, and perform its first synchronization. The status of this update will be recorded in the Recent Updates section in the device panel. Before moving on, you should ensure that the synchronization was successful.
Configuring IAM and 2FA solution¶
Our team has tested the following solutions to work with Threat Response.
- Identity Management and Web SSO
- Okta
- OneLogin
- Ping Identity
- Centrify
- Microsoft Azure SSO
- Multi-Factor Authentication
- Duo Security
- RSA SecureID
- SafeNet
- Symantec 2FA
Please, follow the configuration steps of these integrating vendor configuration guides in order to enable proper integration. The major step is to make sure IAM or 2FA vendors are picking up the security group information from the AD and applying the desired security policies.