Threat Response - Integration with Juniper Secure Analytics¶
The Juniper Secure Analytics SIEM platform serves as a log repository, and allows administrator’s to build correlation rules to generate alerts when suspicious activity is detected in the logs. These alerts can be forwarded to Threat Response, and managed through the Threat Response incident management workflow. This document covers all aspects of Threat Response integration with the Juniper Secure Analytics platform.
Forwarding Alerts to Threat Response¶
Juniper Secure Analytics can forward alerts to the Threat Response platform to be managed using Threat Response’s incident management workflow. The steps below detail the process of creating a Juniper Secure Analytics alert source in Threat Response, and configuring Juniper Secure Analytics to send the alerts to Threat Response. With this configuration completed, Juniper Secure Analytics will begin sending alerts to Threat Response via syslog to generate incidents in the Threat Response platform.
Note
In order for Juniper Secure Analytics to send event data to Threat Response, port UDP/514 must be open on any firewalls between Juniper Secure Analytics and Threat Response.
Creating an Alert Source in Threat Response¶
You must first create an event source in Threat Response to receive alerts from the Juniper Secure Analytics system. The steps below outline the source creation process.
- Log in to Threat Response
- Navigate to the Sources page
- Click the blue Add (+) button next to Sources to bring up the New Source panel
- Set the following fields:
- Type:
Juniper Secure Analytics - Name:
<alert_source_name> - Description:
<description> - Link Events:
<checked>
- Type:
- Save changes.
Configuring Juniper Secure Analytics to Log Alerts for Security Rules¶
Juniper Secure Analytics routes alerts to Threat Response by way of its local syslog service. To forward alerts to Threat Response, you must edit your security rules in Juniper Secure Analytics, and configure them to log to the local syslog when triggered.
To enable logging for your existing Juniper Secure Analytics rules:
- Log in to the Juniper Secure Analytics web interface.
- Navigate to the
Offenses>Rulespage. - Create or edit a rule that you would like to forward to Threat Response.
- In the
Rule Responsesection of the rule creation wizard, check the box toSend to Local SysLog.
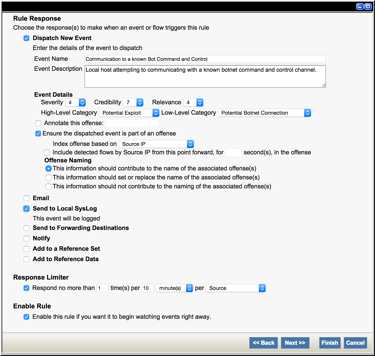
- Click
Finishto save your rule settings.
Enabling Syslog Forwarding in Juniper Secure Analytics¶
With Juniper Secure Analytics logging alets to its local syslog, we can configure syslog-ng to forward the alerts to Threat Response. The following steps outline the process for updating the syslog-ng configuration file to monitor for relevant alerts, and forward them to Threat Response.
Note
The steps below must be performed on all Juniper Secure Analytics consoles and collectors in your environment.
To enable syslog forwarding in Juniper Secure Analytics:
- SSH into Juniper Secure Analytics as a user with elevated permissions
(Example: root) - Use a text editor to modify /etc/syslog-ng/syslong-ng.conf.default.
# vi /etc/syslog-ng/syslog-ng.conf.default- Create a new section at the end of the configuration file for Threat Response and input the following:
# Threat Response Alert Forwarding
filter threatresponse { facility(local1) and level(info) and match("<pattern>" value("MESSAGE")) };
destination PTR_appliance { udp(ptr.example.com port(514)); };
log { source(local); filter(threatresponse); destination(PTR_appliance); };Note
Replace <pattern> with a RegEx that matches the Juniper Secure Analytics rule name(s), and ptr.example.com with the IP or hostname of Threat Response.
- Save the configuration changes.
- Restart syslog-ng.
# /etc/init.d/syslog-ng restartUpon completion of the configuration, Juniper Secure Analytics will begin forwarding alerts to Threat Response. It is recommended to test the configuration by triggering one of the rules, and confirming that the alert is routed to Threat Response.