Threat Response - Integration with Cisco OpenDNS¶
OpenDNS enables network administrators to block unwanted or malicious websites for users across their networks using OpenDNS’s DNS sink-holing capabilities. By integrating Threat Response with OpenDNS, administrators can automatically push malicious websites and domains reported in security alerts to the OpenDNS service, effectively blocking new threats as they are reported.
This document covers the configuration process for linking Threat Response to the OpenDNS Service, and mapping Threat Response lists to OpenDNS.
Mapping Lists to OpenDNS¶
Proofpoint Threat Response can automatically synchronize hosts and domains reported in security alerts to OpenDNS, enabling the service to block malicious websites as they are reported.
Create a Custom Integration in OpenDNS¶
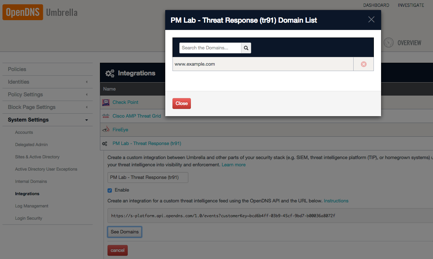
The first step in mapping a Threat Response list to OpenDNS is to create a new custom integration in OpenDNS. Upon creation, OpenDNS will generate a unique URL that can be copied to Threat Response as a destination for the list mapping.
To create a new custom integration in OpenDNS:
- Log in to the OpenDNS web portal
- Click on the
Configurationtab - In the left-hand navigation panel, navigate to
System Settings>Integrations - Click add a new custom integration
- Provide a name for the new integration (e.g., “Proofpoint Threat Response”)
- Click
createto save the new custom integration
- The integration is disabled by default. To enable it:
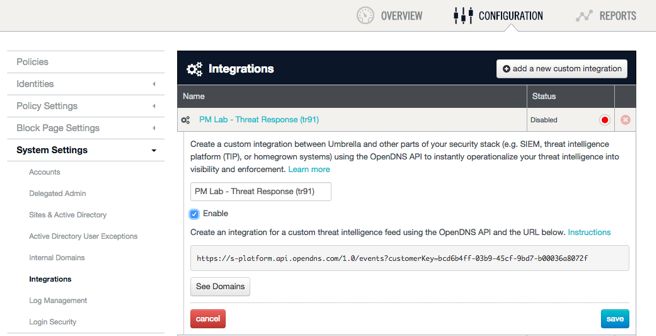
- Click on the new integration object to expand its configuration (see above)
- Check the
Enablecheckbox to enable the integration - Click
save
- Copy the integration URL:
- Click on the new integration object again to expand its configuration
- Copy the integration URL to your clipboard—we will paste this into Threat Response in the next step
Create an Internet Service in Threat Response¶
With the Custom Integration prepared in OpenDNS, you can now create an Internet Service object in Threat Response that will represent the OpenDNS service.
To create a new Internet Service:
- Log in to Threat Response
- Navigate to the
Devices>Internet Servicespage - Click on the
Add (+)button to create a new Internet Service
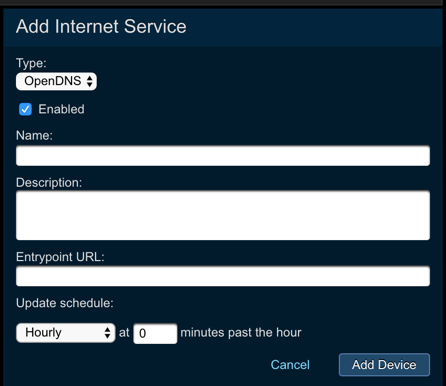
- Configure the following settings:
- Type: OpenDNS
- Name:
<provide a name for the service> - Entrypoint URL:
<paste the integration URL> - Update this device:
Every Minute - Description:
<service description>
- Save changes
Map a List from Threat Response to OpenDNS¶
With Threat Response now linked to OpenDNS, you can create a list mapping that will tell Threat Response which list to keep in sync with OpenDNS.
Note
Only one list can be mapped to an OpenDNS Internet Service in Threat Response. To map multiple lists to OpenDNS, repeat steps 1 & 2 above to create additional custom integration instances.
To map a list from Threat Response to OpenDNS:
- Click on the
Add (+)button in the List Mappings section of your OpenDNS Internet Service in Threat Response
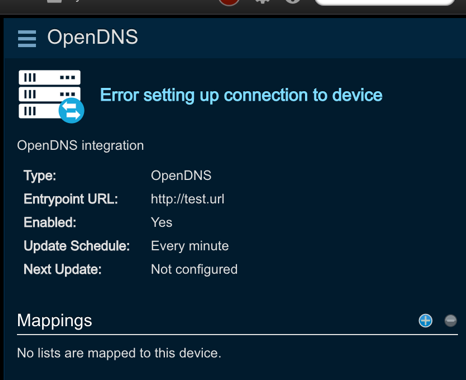
- In the New Device Mapping window, select the list that you want to map to OpenDNS
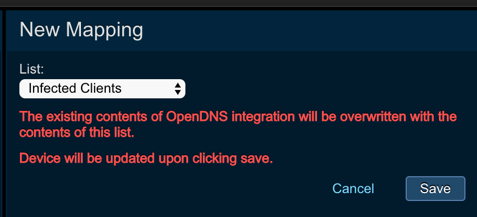
- Save Changes
Upon saving your list mapping, Threat Response will connect to the integration URL, and synchronize its local list to OpenDNS. From this point forward, Threat Response will update OpenDNS based on the update schedule defined in the Internet Service in Threat Response (Step 2 above).
To confirm that the mapping was successful, click the See Domains button in OpenDNS to view a list of items synchronized from Threat Response.