Threat Response - Integration with Palo Alto Networks¶
Proofpoint Threat Response can interface with Palo Alto Networks devices and services to share information about threats seen on the network. This document covers integration with both Palo Alto Networks firewalls, and the Palo Alto Networks WildFire service.
As an event source, Palo Alto Networks devices can forward IDS & WildFire alerts to Threat Response for management and review. Threat Response will lookup additional details about the alerts, such as a user’s LDAP attributes and reputation information for IPs, and will present the data in an easy-to-digest format along with an incident management workflow.
Information can also be communicated back to Palo Alto Networks devices for use in security policies and URL filtering rules. Administrators can map Threat Response lists to Address Groups in Palo Alto Networks devices, and specify a synchronization interval to keep the information up-to-date. Items can be added or removed from these lists automatically using Match Condition rules in Threat Response, or manually using Threat Response’s incident workflow.
Sending PAN Alerts to Threat Response¶
Palo Alto Networks firewalls can be configured to forward security alerts to Threat Response for additional analysis and to provide an alert workflow. Alert types that can be forwarded to Threat Response include IDS alerts generated by the Palo Alto Networks device, as well as malware alerts from the Palo Alto Networks WildFire service.
Create an Event Source in Threat Response¶
You must first create an event source in Threat Response to receive alerts from the Palo Alto Networks system. The steps below outline the event source creation process.
To create a Palo Alto Networks event source:
- Log in to Threat Response
- Navigate to the
Sourcespage - Click the blue
Add (+)button next toSourcesto bring up theNew Sourcepanel
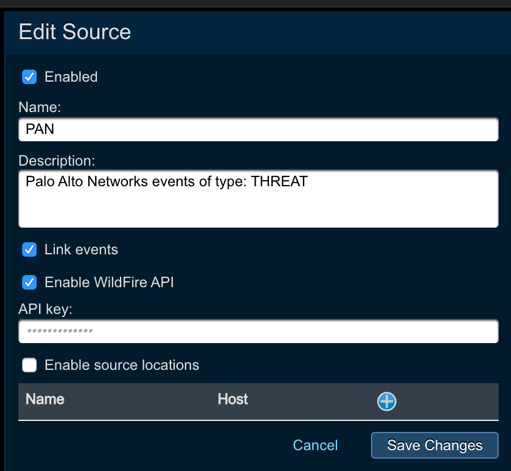
- Set the following fields:
- Type:
Palo Alto Networks - Name:
<event_source_name> - Description:
<description> - Link Events:
<checked> - Enable WildFire API: Check this option to enable WildFire API lookups
- API Key: Input your WildFire API key here
- Type:
Savechanges.
Note
Due to the syslog nature of these alerts, Threat Response only allows the creation of a single Palo Alto Networks event source.
Create a Syslog Server Profile in PAN¶
A Syslog Server Profile must be configured to forward alerts to Threat Response. Because Threat Response only receives a subset of the total syslog data that Palo Alto Networks generates—Threat and WildFire alerts—a new Syslog Server Profile should be created to be distinguished from other profiles, which may also receive Traffic syslogs.
Note
This new Syslog Server Profile will include Threat Response, as well as any other systems that should also receive security alerts from the PAN.
To create a new Syslog Server Profile:
- Log in to the Palo Alto Networks device
- Click the
Devicetab - Navigate to
Server Profiles>Syslogin the left-hand navigation menu
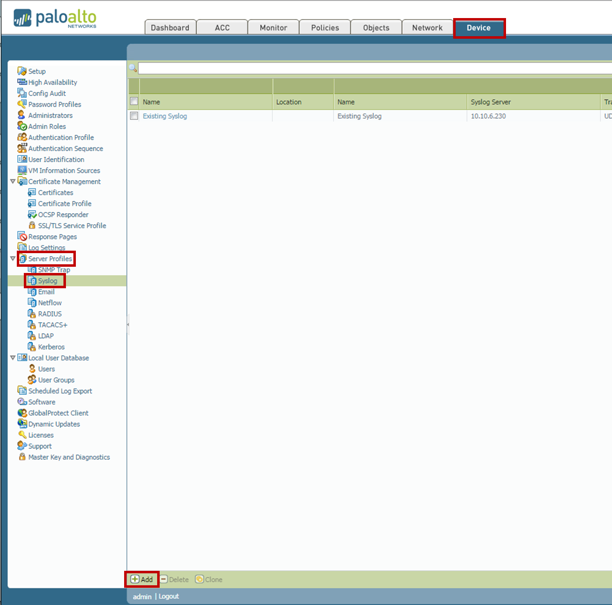
- Click
Addat the bottom of the page to open the Syslog Server Profile dialog
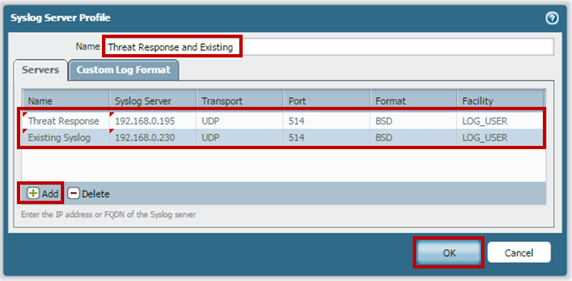
- Create a name for the new profile
- Click
Addat the bottom of the popup to add Threat Response to the profile
Note
The syslog listening port on Threat Response is UDP/514.
- Repeat step 6 above for other systems that should receive security alerts from PAN
- Click
OKto save the new profile
Update PAN’s Log Forwarding Profile¶
Modify the existing Log Forwarding Profile to route security-based alerts to the new Syslog Profile created in Step 2. Security alerts that can be forwarded to Threat Response include Threat and WildFire alert types.
To modify the Log Forwarding Profile:
- Navigate to
Objects>Log Forwardingin the left-hand navigation menu - Click on the current Log Forwarding Profile used by the Palo Alto Networks device to open the Log Forwarding Profile dialog box
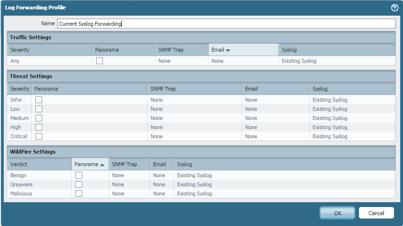
- Under Threat Settings and WildFire Settings, update the
Syslog field(s)to reference the new Syslog Server Profile created in Step 2.
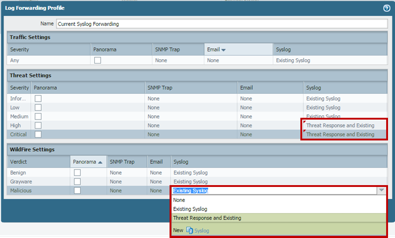
Note
Security alerts can be extremely high-volume. It is recommended to forward only the High and Critical alerts in Threat Settings, and only Malicious alerts in the WildFire configuration to Threat Response.
- Click OK to save the changes.
Assign Log Forwarding Profile to a Security Policy¶
The Log Forwarding Profile must be referenced in a policy on the Palo Alto Networks device before syslog alerts will be generated. This step should only be completed if you have not yet created policies on your Palo Alto Networks device that utilize the Log Forwarding Profile.
To assign the Log Forwarding Profile to a policy:
- Navigate to
Policies>Securityin the Palo Alto Networks device. - Locate the appropriate policies that should generate alerts to Threat Response, and have a threat profiles assigned to them.
Note
Check the Profile column to determine if any threat profiles have been assigned.
- Click on the icons in the Options column to pull up the policy options for the selected policy.
- Select the appropriate Log Forwarding profile in the Log Forwarding drop-down.
- Click
OK.
Once you have configured Syslog and associated the Log Forwarding Profile to a security policy, events matching the Log Forwarding Profile will be sent to Threat Response. You can confirm that events are being received by viewing the Sources page in Threat Response.
Mapping Block Lists to PAN¶
Threat Response can synchronize its local lists to Address Groups and URL profiles in the Palo Alto Networks device. As items are added to the list in Threat Response, the PAN will be automatically updated with this new information.
Create a Palo Alto Networks Device in Threat Response¶
To map a Threat Response list to your Palo Alto Networks device, you must first tell Threat Response how to communicate with that device.
To create a Palo Alto Networks device in Threat Response:
- Log in to Threat Response
- Navigate to the
Devicespage - Click on the
Network Devicessub-tab - Click the blue
Add (+)button next to Network Devices to bring up the New Network Device panel
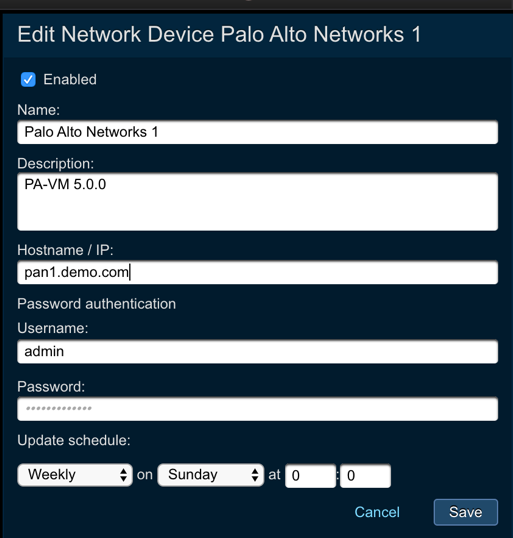
- Configure the following fields:
- Type:
Palo Alto Networks - Name:
<device_name> - Hostname / IP: The IP or hostname of the device
- Username: The username used to login to the device
- Password: The password used to login to the device
- Update this device: Define the update schedule
- Description:
<device_description>
- Type:
Savechanges
Map a List to the Palo Alto Networks Device¶
Once your Palo Alto Networks device has been created in Threat Response, you can begin mapping Threat Response lists to it.
Note
When a list mapping is created, Threat Response will overwrite the destination object with the information in its local list.
To map a list to a Palo Alto Networks device:
- Click on the device that you want to map a list to.
- In the
Device Detailspanel, click the blueAdd (+)button next toList Mappings to open theNew Device Mappingpanel - Using the
Listdropdown, select the list that you want to map to the PAN - Input a
Group Nameto tell Threat Response what to name the Address Group - Save changes
Once saved, Threat Response will connect to the PAN and create the Address Group. If the group already exists, it will be overwritten with the items in the Threat Response list.
Configuring Dynamic Block Lists¶
Palo Alto Networks devices offer a synchronization feature called Dynamic Block Lists (DBL), that enable it to pull lists of IPs from another device into a local object. This “pull” method eliminates the need for Threat Response to push updates to the firewall, eliminating the need to commit changes to the PAN device.
Note
This method of synchronization may be preferred in environments where commit / change management is restricted to a specific time of day, or restricted to specific machines or users.
Configure List Publishing in Threat Response¶
To use the Dynamic Block List capabilities in PAN, you must first publish the list that you want to synchronize in Threat Response. List publishing allows the list to be queried remotely via a URL.
To publish a list in Threat Response:
- Navigate to the
Listspage in Threat Response - In the
Liststable, select the list you would like to publish - In the
List Detailspanel, open the menu and selectEdit - Place a checkmark next to the
Publishoption to publish the list Savechanges
Now that the list has been published, it can be accessed via URL. Click the Show published URL link from the list details to view the available URLs.
Note
Be sure to copy the List URL after publishing so that it can be pasted into the PAN configuration.
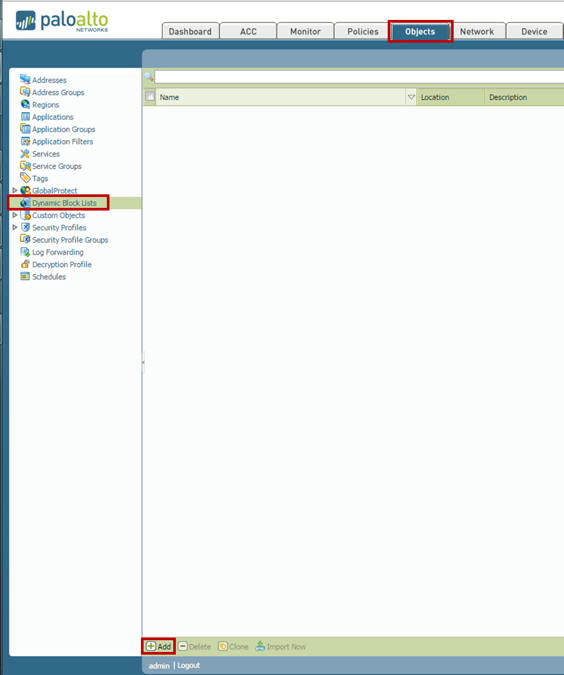
Create a Dynamic Block List in PAN¶
Dynamic Block Lists can be configured on the Palo Alto Networks device to pull block lists from Threat Response.
To configure dynamic block lists:
- Log in to your Palo Alto Networks device UI.
- Navigate to
Objects>Dynamic Block Lists. - Click the
Addbutton to create a newDynamic Block List.
- Input the following details:
- Name:
<dbl_name> - Description:
<dbl_description> - Source:
<list_url_from_threat_response> - Repeat:
<define_update_schedule>
- Name:
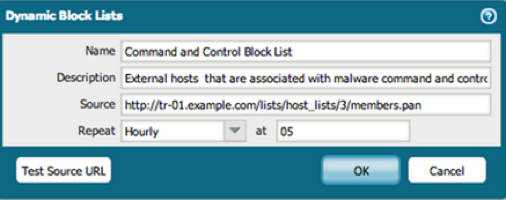
- Click
OKto save the new Dynamic Block List.
The Palo Alto system will now update this Dynamic Block List on the defined schedule. The Dynamic Block List is now ready to be used when creating policies on the Palo Alto device.