Threat Response - Integration with Juniper SRX¶
This document covers all aspects of Threat Response integration with Juniper SRX Series Service Gateways. The Proofpoint Threat Response platform can integrate with Juniper’s SRX Series in the following ways:
- As an Enforcement Device
Juniper SRX can be used to prevent network-based access to malicious hosts, or to restrict access to certain areas of the network for infected users. Threat Response can place suspicious hosts reported in security alerts into a Threat Response block list, which is then pushed up to the SRX as an address group to be used when building policies.
Configuring a Juniper SRX Device¶
The steps below detail the process for configuring Threat Response to map a local block list to an address group in a Juniper SRX device. With the mapping in place, policies can be created on the SRX that reference the address group managed by Threat Response.
Create a Host List in Threat Response¶
The first step in enabling synchronization with Juniper SRX is to create a Host List in Threat Response to map to an address group on the SRX. Follow the steps below to create the Host List in Threat Response.
- Log in to Threat Response.
- Navigate to the
Listspage. - Click on the
Host Listssub-tab to manage your Host Lists. - Click the blue
Add (+)button next to Lists to bring up the New Host List panel. - Set the following fields:
- Name:
<list_name> - Description:
<list_description>(Optional) - Publish:
<checked_or_unchecked>(Optional)
- Name:
Savechanges.
Note
List Publishing enables remote polling of a list in Threat Response via HTTP/S. It is not required for a Juniper SRX configuration.
Create a Juniper SRX Device¶
In order to map a Threat Response list to your Juniper SRX device, you must first tell Threat Response how to communicate with that device.
- Log in to Threat Response
- Navigate to the
Devicespage - Click on the
Network Devicessub-tab - Click the blue
Add (+)button next to Network Devices to bring up the New Network Device panel
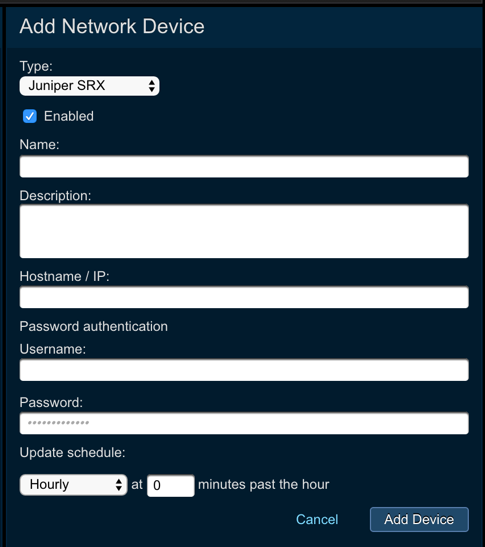
- Set the following fields:
- Enabled: enable the device after the configuration is saved
- Name: provide device name
- Description: provide device description
- Hostname / IP: provide IP or hostname of the device
- Authentication: you can choose to enable password authentication, where you need to provide username and password
- Update this device: define the update schedule by choosing the appropriate option from the drop down menu
Savechanges.
Map a List to the Juniper SRX Device¶
Once your Juniper SRX device has been created in Threat Response, you can begin mapping lists to it. These will appear as Address Sets or Prefix Lists in the SRX.
Note
Once saved, Threat Response will automatically connect to the SRX, and attempt to create the group on the device. If the group already exists, it will be overwritten with the items in the Threat Response list.
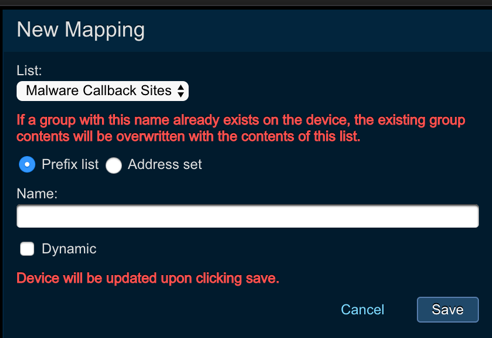
To map a list to a Juniper SRX device:
- Log in to Threat Response.
- Navigate to the
Devicespage. - Click on the
Juniper SRXdevice that you want to map a list to. - In the
Device Detailspanel, click the blueAdd (+)button next toList Mappingsto open theNew Device Mappingpanel. - Select the appropriate list from the List dropdown.
- Input a
Group Nameto tell Threat Response what to name the address group in the Juniper SRX. Savechanges.