About Threat Response¶
What is Threat Response?¶
Proofpoint Threat Response
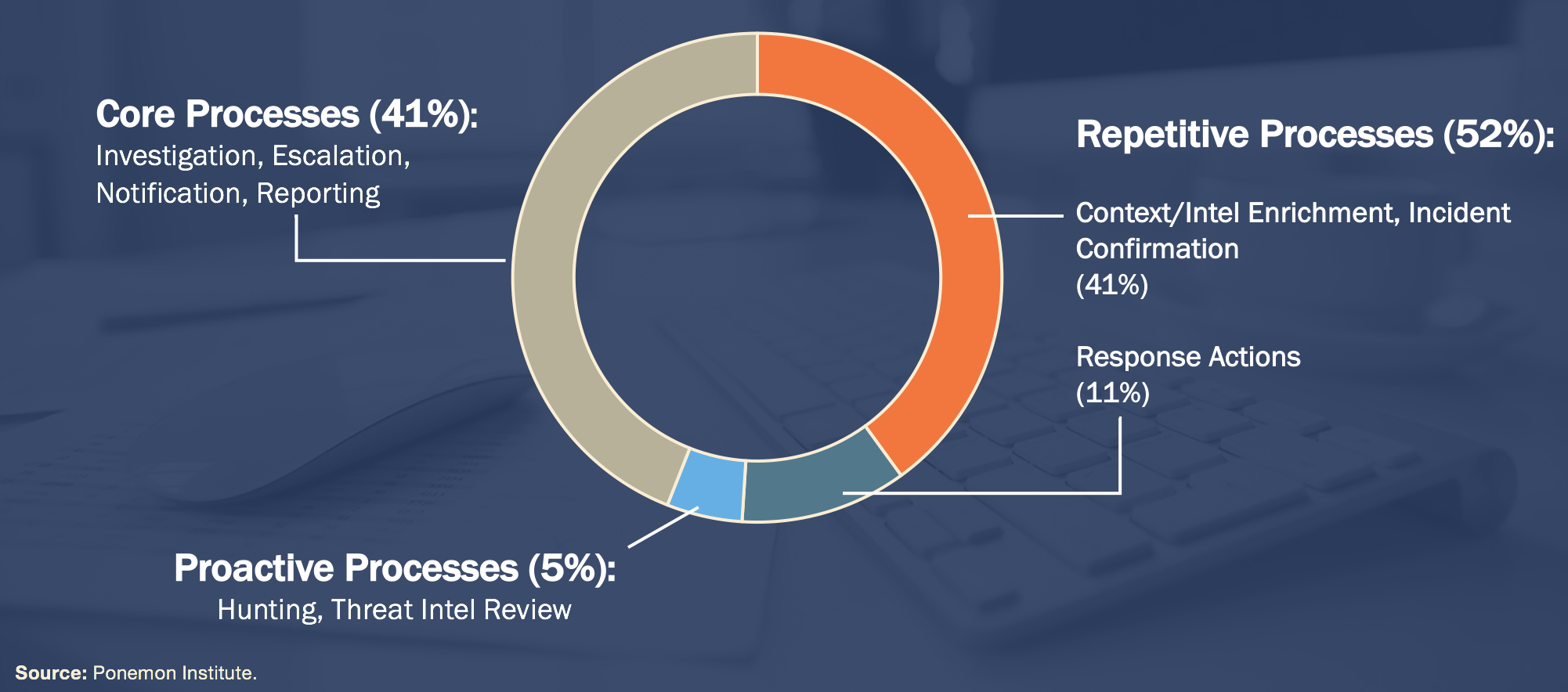
Today’s security industry is plagued with repetitive processes and inefficiencies stemming from manual execution of tasks. Present day SOCs are characterized by multi-vendor environment, shortage of skilled personnel, alert overload, and human error. All these factors contribute to increasing the overall volume of security routine work.
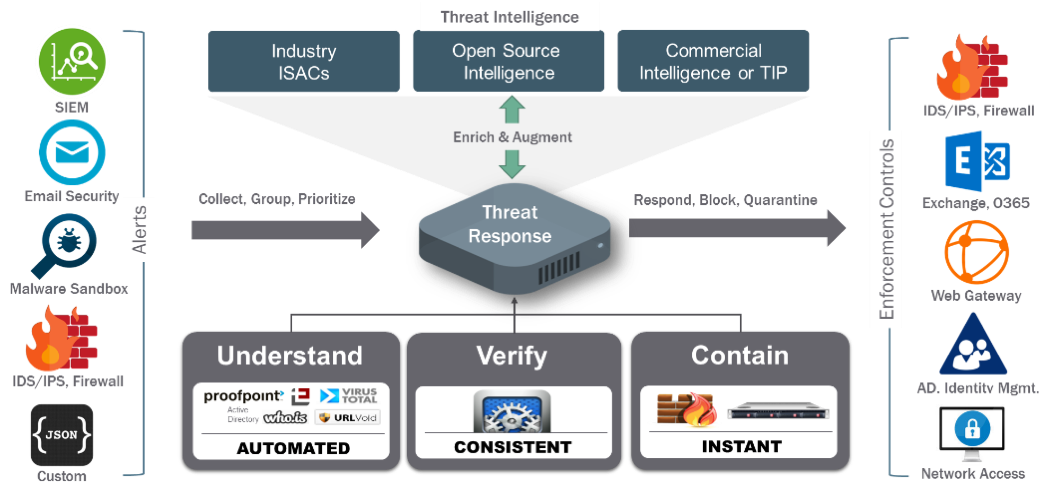
By developing a solution that actively links multi vendor security enforcement points to a variety of security intelligence offerings, Threat Response transforms traditionally rigid, static security devices into dynamic defenses capable of responding automatically to malicious attacks in real time.
Threat Response allows SOC teams to:
- Understand & enrich security alerts - by collecting alerts from various sources, Threat Response automatically enriches each alert in the matter of seconds with rich and vital context, such as OSINT data, user-IP mapping, as well as external Threat Intelligence, so that analysts can quickly triage and prioritize incoming events.
- Verify infections - Threat Response can automatically verify alert data by collecting triage packages from endpoints and correlating information such as mutexes, registry keys, and processes found in the incoming forensics reports with those found on the endpoint. The process saves analysts hours and helps to confirm whether the infection has indeed reached the endpoint.
- Respond to incidents - Threat Response offers a number of responses out of the box, such as adding host and users to enforcement lists, quarantining emails, or initiating custom API responses to 3rd party products.
What documentation is available?¶
This documentation portal provides a comprehensive overview of how to install the system, operate it, and use it to effectively respond to security incidents. Below, you can see how the information is structured.
| Document | Description | Audience |
|---|---|---|
| Installation guide | The Installation guide provides information on how to get Threat Response up and running in your environment. The Installation guide includes the list of hardware requirements, all the major steps to install the Threat Response image in a VMware environment, and configure required bootstrap services. | Admin |
| Administration guide | The Administration guide provides a detailed configuration overview of all Threat Response functionality. You can learn how to operate the Management Console, conduct service operations such as backup and clustering, as well as how to navigate setting and configure platform features. | Admin |
| User guide | The User guide provides information on how to operate Threat Response, use its features, as well as navigate the UI. You will learn how to generate responses, write match conditions, etc. | Analyst |
| Integrations | Threat Response offers numerous 3rd party integrations out of the box. Integrations lists the currently supported integrations and provides links to guides that describe how to configure them. | Admin & Analyst. |
| Extensibility | The Extensibility section provides information on how to customize Threat Response, use custom responses, and operate the built-in REST API. | Admin & Analyst |
| Release notes | The Release notes offer insights into new functionality and enhancements. | Admin |