Content Rules - Increasing Automation With Context¶
PTR/TRAP 5.3 enables security teams to contextualize their data into the CLEAR automation pipeline by providing the capability to define content rules in match conditions. This capability allows security teams to automate processing of a large number of internal emails in addition to known vendor emails as well as creating separate workflows for executive submissions, among other use cases.
What Are Content Rules¶
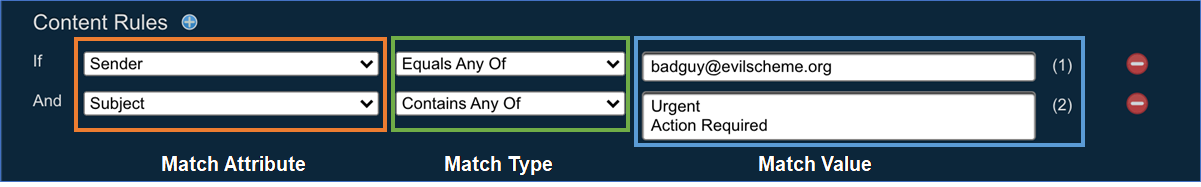
Content rules are essentially criteria based on message content, such as email headers, URLs, attachments and other attributes of a message. Three components characterize content rules:
-
Match Attribute: Which attribute should be matched? This field is used to define the section of the message content on which the rule matches. It supports a preset list of attributes and can be extended to include additional message headers as described in the Adding a Custom Email Header to Content Rules section below. The preset list of message attributes is as follows.
- Sender
- Subject
- Recipient
- Attachment Name
- Attachment Hash
- Body Content
- URL
- X-Originating-IP
- X-Connecting-IP
- Content-type
- Return-Path
- Received
- Message-ID
- Reply-To
- X-Auth-Sender
- Custom Headers (See Adding a Custom Email Header to Content Rules below.)
-
Match Type: How should the attribute be matched? This field defines how the match should be evaluated, i.e. whether the match should be exact or a wildcard pattern match. The field supports the following values.
- Equals Any of
- Contains Any of
- Begins with Any of
- Ends with Any of
Note
Irrespective of match type, case sensitivity has no bearing on the evaluation of matches.
-
Match Value: What value of the attribute constitutes a match? This field specifies the value that is being searched. It supports
- singular entries and
- line-separated lists.
Example Use Cases¶
While use cases and workflows are specific to every organization, note the following set of examples to give you some ideas for setting up content rules.
- Auto-Closing Large Numbers of Internal Emails Largely distributed internal emails asking for sensitive information such as financial details may get flagged for manual review by Proofpoint CLEAR; however, since they may be sent to many employees, this can often lead to a heavy workload for the security team. If these emails can be identified as legitimate communication with context available to the security team, they can be auto-closed using content rules.
A largely distributed internal email sent by a legitimate stakeholder
An example content rule used to automate processing of the largely distributed internal email
- Separate Workflow for Executive Submissions Executive submissions are usually considered higher risks to your organization. Content rules allow you to set up a separate workflow for abuse mailbox submissions made by executives in your organization.
A suspicious email reported by the CEO
An example content rule used to set the severity to “high” for submissions by the CEO, CFO and other executives who get flagged for manual review
- Auto-Closing Known Vendor Emails Emails from known vendors can lead to repetitive work for security teams as the emails are repeatedly submitted over time. Content rules can be used to automate closing of such submissions.
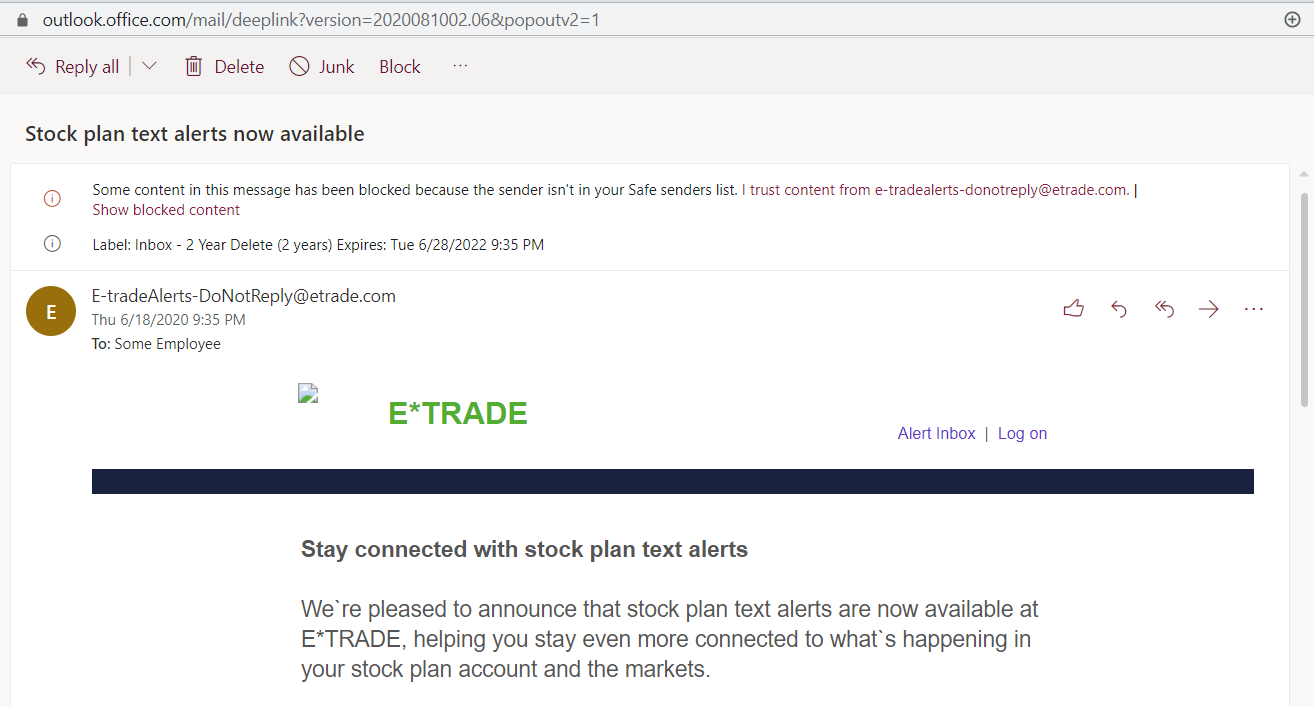 An email from a recognized vendor
An email from a recognized vendor
An example content rule used to auto-close incidents coming from a recognized vendor and IP address
Important Considerations¶
- Match conditions with content rules are treated as special cases and take precedence over match conditions without content rules
- An alert that matches a content rule match condition at a given time of execution will not be evaluated against any non-content rule match conditions.
- A content rule match condition that triggers at the time a new alert is received may prevent an email from being submitted to Proofpoint Threat Intelligence for analysis, especially for messages forwarded to the abuse mailbox rather than submitted using PhishAlarm.
Recommendations¶
- We recommend triggering content rule match conditions after Proofpoint has analyzed an email (checkbox for after an email is analyzed). This ensures that compromised email accounts and spoofed addresses do not get a free pass through the content rule workflow.
- Content rule match conditions that aim to auto-close incidents without quarantining messages should be triggered only if the abuse disposition is “Unknown,” “Low Risk,”’ or “Bulk.” If, after Proofpoint’s analysis of a message, it receives a “Spam,” “Malicious,”’ or “Suspicious” abuse disposition, it is very likely to present a threat and should not be closed out without a quarantine action.
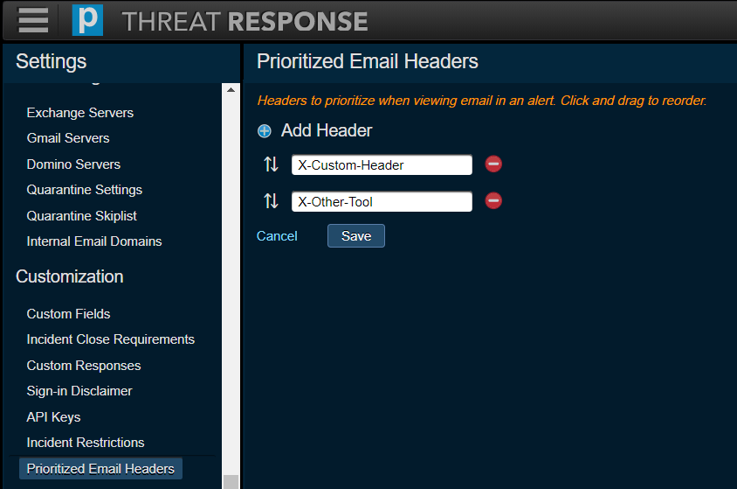
Adding a Custom Email Header to Content Rules¶
Custom headers can be added to content rules in the Prioritized Email Headers section on the System Settings page (System Settings > Customization > Prioritized Email Headers).