Threat Response - Upgrade Guide¶
This chapter describes the process to be followed when upgrading an older version of Threat Response (3.x or 4.x) to version 5.x.
If you are looking to upgrade between 5.x versions, click here.
If you are looking to upgrade Threat Response on AWS, click here.
Overview¶
Proofpoint Threat Response (PTR) and Threat Response Auto-Pull (TRAP) 5.x include major improvements to their Linux-based platform. Thus the process for upgrading the virtual appliance has effectively changed. A PTR/TRAP 5.x version must be configured as a new virtual appliance to migrate data from the earlier version of the application.
Upgrade Steps¶
To begin the process, follow these instructions.
Backing Up the Data on the Existing PTR/TRAP Instance¶
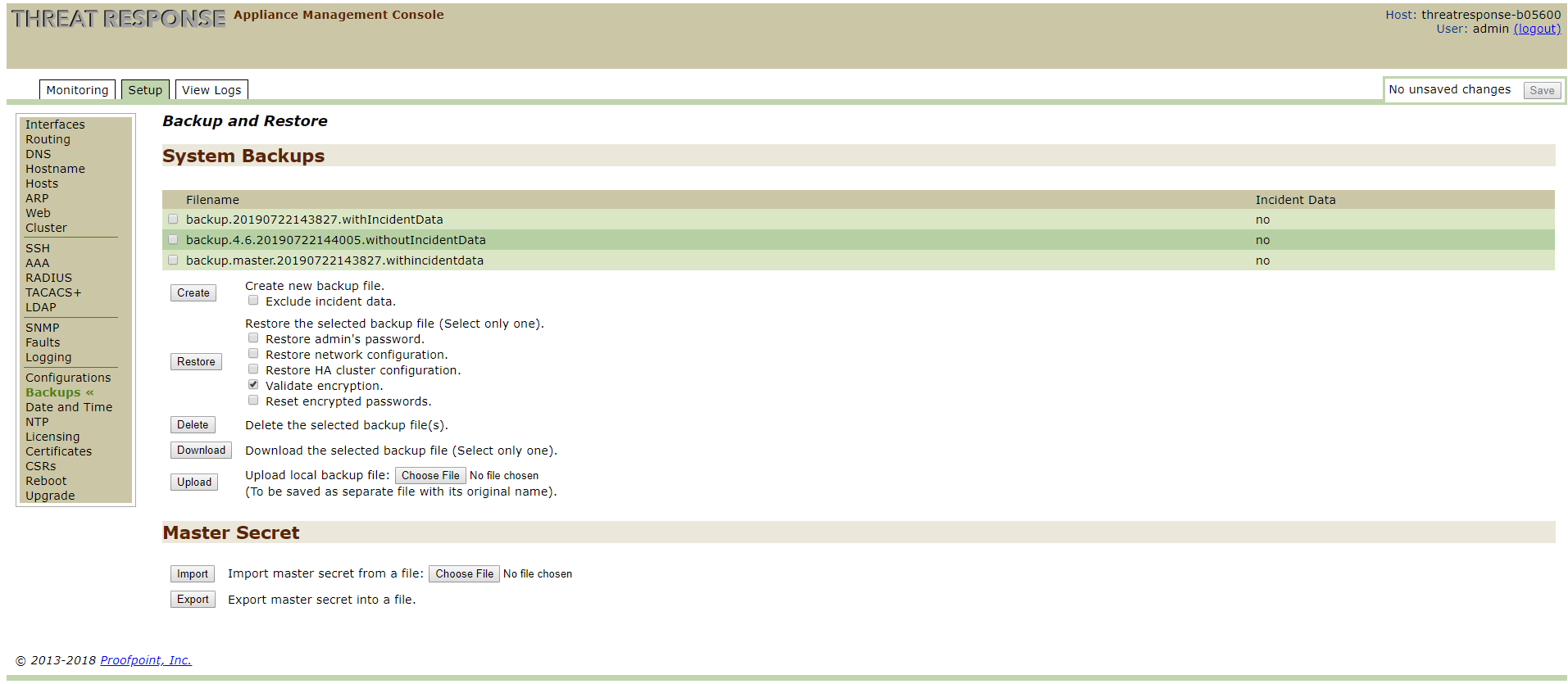
- Log in to the Appliance Management Console: https://PTR-Instance:8080/
-
Proceed to Setup, then Backups.
-
Make a backup of the file (with incident data). Download the data.
- Export the Master Secret into a file. Download the Master Secret.
Note
Be sure to disable any configured alert sources pertaining to versions 4.x before you back up any data–otherwise it might come to pass that 4.x and 5.x appliances will operate synchronously and thus any alerts would be duplicated. (Refer to the Threat Response Administration Guide for “disabling” instructions.)
Moreover, if the alert sources are enabled on both these appliances, then both will poll/consume the alerts and start to execute any match conditions. Thus it is not advisable to create a “race” condition between two instances of Threat Response (the execution of the same response for match conditions on sources) because ultimately, that could lead to a successful quarantine on one instance but a failure on another instance of Threat Response. Such a situation could lead to skewed quarantine reports on the appliances.
Configuring the New PTR/TRAP 5.x Instance¶
- Set up a new virtual machine by using the PTR/TRAP 5.x OVA file. See the Installation Guide.
- Ensure that the virtual machine provides networking to Overcast (https://overcast.proofpoint.com/), a Proofpoint-owned validation service, at the time that you are setting up the system networking in the Initial Configuration Wizard.
Note
If the virtual machine does not have network connectivity to Overcast (https://overcast.proofpoint.com/), you will be unable to validate the licenses on the system in subsequent steps.
Migrating the Application Data to the New PTR/TRAP 5.x Instance¶
-
Log in to the Appliance Management Console: https://New-PTR-Instance:8080
-
Proceed to Maintenance, then Backups.
-
Upload the backup file. (Note that it was downloaded from the existing PTR/TRAP instance.)
-
Upload the Master Secret file. (Note that it was downloaded from the existing PTR/TRAP instance.) This operation can take a few minutes to complete.
Important
Uploading the master secret causes a restart of all the services. Please wait for the services to come back up before proceeding with next steps.
-
Select the uploaded backup file, then ensure that Validate Encryption is checked. Click on Restore. (Wait for the data restoration to complete.) The process can take several minutes to several hours depending on the size of your database.
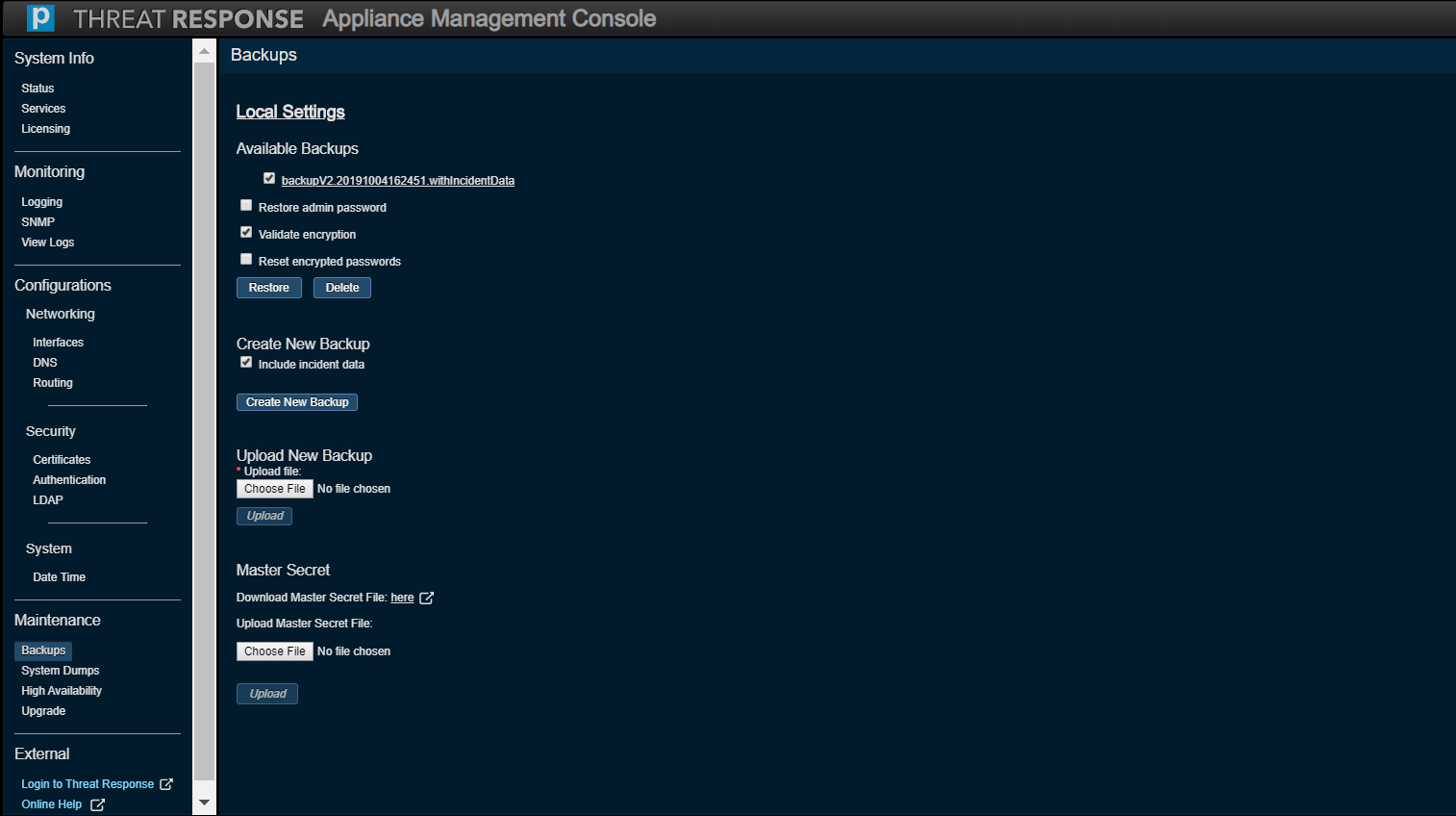
At this point, configurations architected in PTR/TRAP (on the application side), as well as the incident data included in the backup, will be restored on the new instance.
Validating the License Keys on the New PTR/TRAP 5.x Instance¶
Proceed to System Info, then Licensing on the Appliance Management Console. (Note that you should see the license keys backed up from the old PTR/TRAP instance under Available License Keys.)
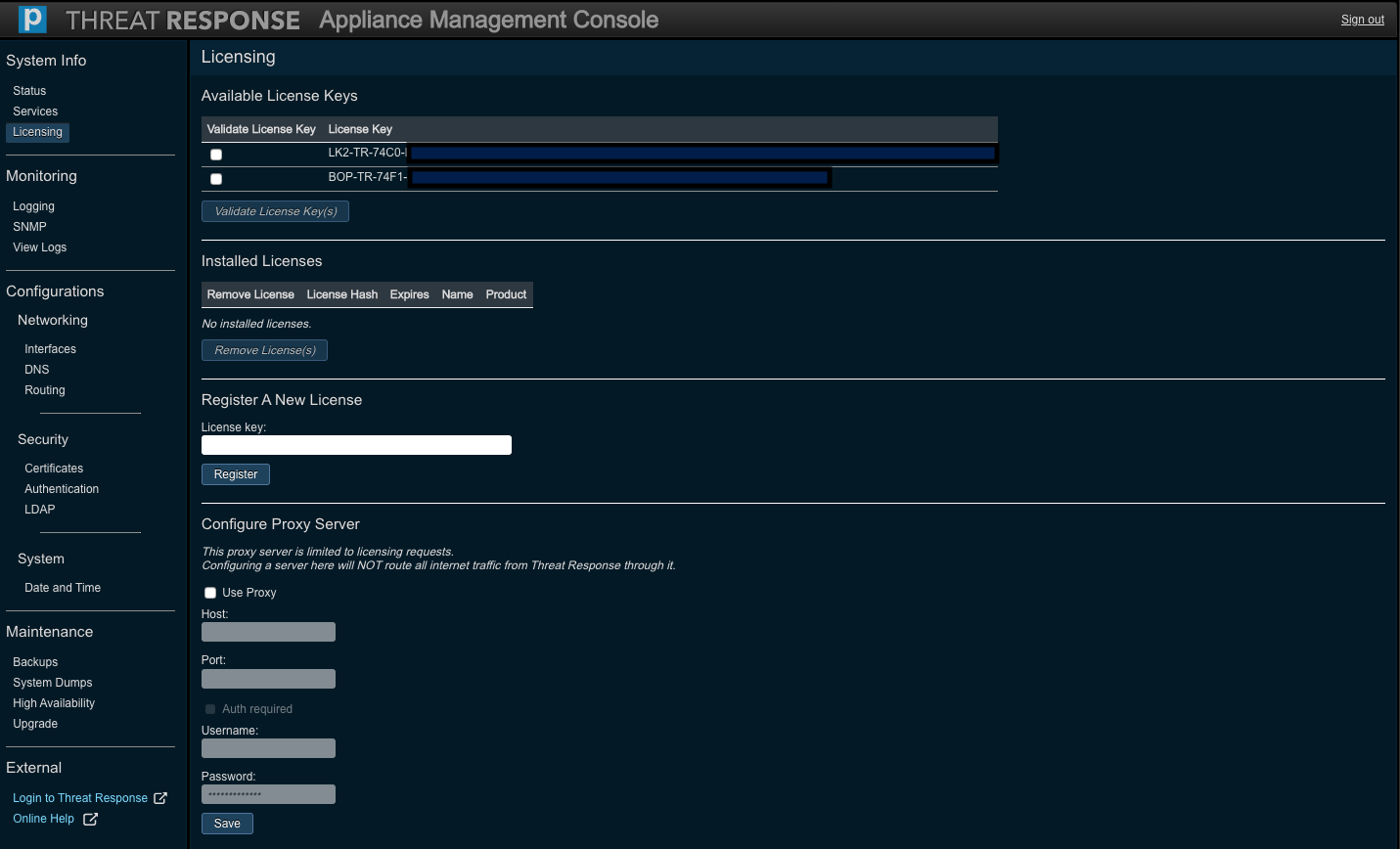
Any licenses backed up from the old PTR/TRAP instance need to be validated with Proofpoint before using PTR/TRAP 5.x. The system will connect to Overcast (https://overcast.proofpoint.com/), a Proofpoint-owned cloud service, in order to validate these licenses.
Tip
Network connectivity from the PTR/TRAP instance to Overcast can be quickly verified by setting up an SSH session into the appliance using the credentials of the admin user and running the following command in the root-level system shell:
curl https://overcast.proofpoint.com/v1/ping
If connectivity succeeds, this command will display a result of pong.
If necessary, connectivity to Overcast can be established via HTTPS proxy server in the network. Be sure to check the Use Proxy option to specify a proxy server hostname or an IP address and a port. If the proxy server requires authentication, check the Auth required option to specify a username and password.
Note
The proxy server specified here is only used for license validation. It is not used for any other inbound/outbound network communication on the PTR/TRAP instance. It is also unrelated to the proxy server configured under System Settings in PTR/TRAP.
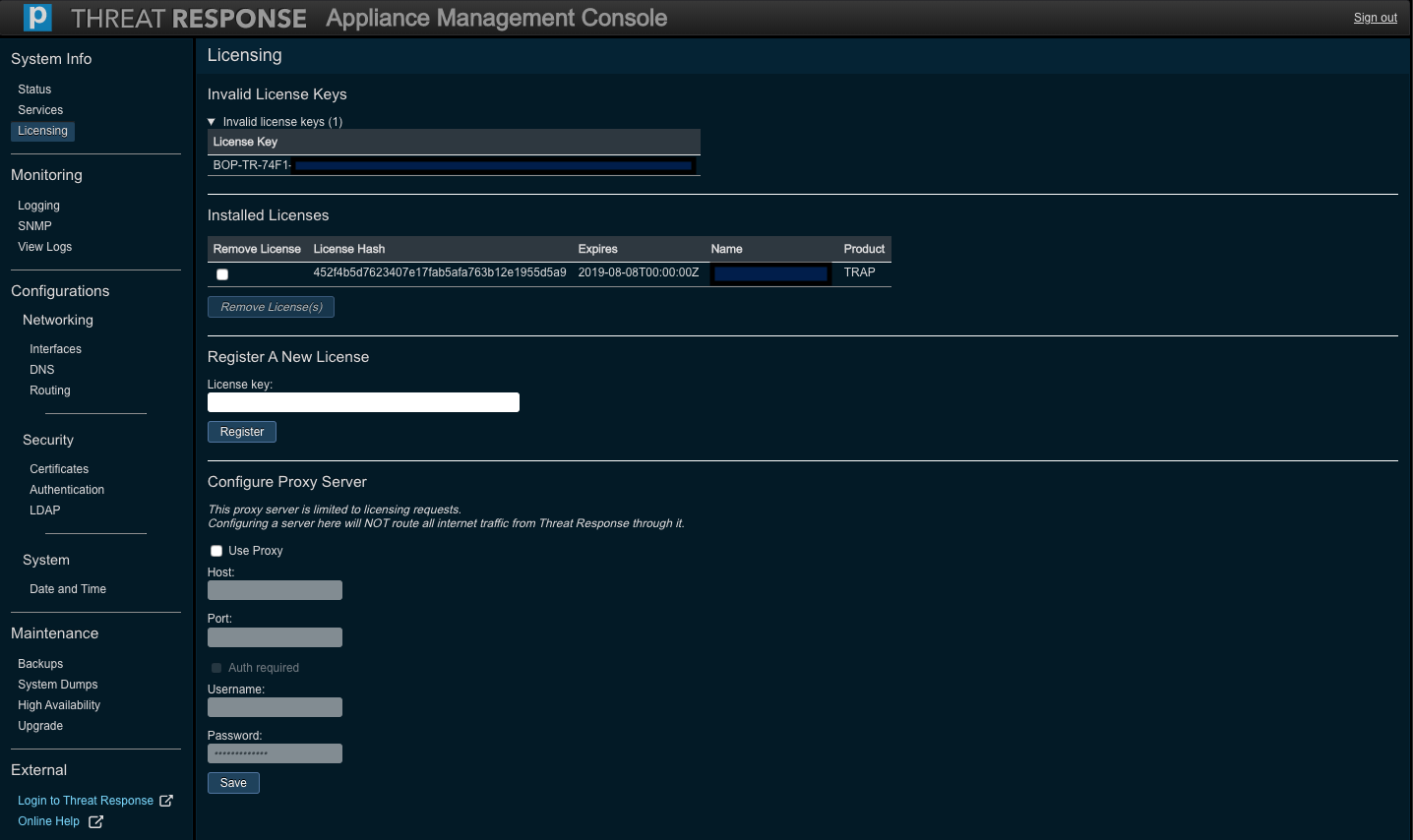
Select the applicable license keys, then press Validate License Key(s) to trigger a validation request. The successfully validated licenses will be applied and displayed under Installed Licenses. Note that each validated license associated with an instance of PTR/TRAP will be accompanied with both a name and an expiration date.
Any license that fails to validate is displayed under Invalid License Keys, which is a collapsable section on this screen. Expand the section to display the invalidated keys as shown below.
If you have any questions or concerns, please create a ticket in the Proofpoint support portal or contact your account representative.
Copying the Management Console Settings¶
Owing to the third-party proprietary nature of the internal storage employed in the old PTR/TRAP instance, you must copy over manually any previously changed settings from the old instance of the Appliance Management Console into the new (PTR/TRAP 5.x) instance.
The following table highlights the sections of the console, for both the old and the new instance, which require careful attention to detail for the purpose of managing changes.
| Old Console Settings | New Console Settings |
|---|---|
| Setup → Interfaces | Configurations → Networking → Interfaces |
| Setup → Routing | Configurations → Networking → Routing |
| Setup → DNS | Configurations → Networking → DNS |
| Setup → Web | Configurations → Security → Authentication |
| Setup → Cluster | Maintenance → High Availability |
| Setup → AAA | Configurations → Security → Authentication |
| Setup → LDAP | Configurations → Security → LDAP |
| Setup → SNMP | Monitoring → SNMP |
| Setup → Logging | Monitoring → Logging |
| Setup → Date and Time | Configurations → System → Date Time |
| Setup → NTP | Configurations → System → Date Time |
| Setup → Certificates | Configurations → Security → Certificates |
Note that with respect to certain screens in the above list, a few fields that were included in the old console may have been omitted in the new console because they are not integral parts of the primary functions of the appliance.
Note
The Default Gateway text box (on the Routing page of the new Appliance Management Console) should not be addressed in any way.
Tip
If you used LDAP-based authentication on an older version of PTR/TRAP, remember to configure the
- LDAP Server and Settings in the Configurations → Security → LDAP screen
- Authentication Order in the Configurations → Security → Authentication screen, to use LDAP.
Given the above specifications, a PTR/TRAP 5.x instance is fully configured to match the old one. Ensure that the migrated data, configurations, and licenses match those on the old appliance. The new instance will now replace the old one.
Note
Previously disabled alert sources, which were migrated, can now be enabled on the new appliance.
As soon as the new instance works as intended, the old instance may be shut down and decommissioned.
Upgrading a Cluster¶
For clustered deployments running an older version of PTR/TRAP, upgrading the cluster of two nodes to PTR/TRAP 5.x must be carried out as follows.
-
Upgrade the primary node of the cluster by following all the steps outlined above. The master secret, database, licenses, and any console settings from the primary node running an older version of PTR/TRAP to the primary node running PTR/TRAP 5.x will be migrated on successful completion of the process.
-
Install the new secondary node of the cluster by following the steps outlined in the Installation Guide. At this point, the PTR/TRAP 5.x secondary node is set up as an independent instance without any data.
-
Follow the steps in the Clustering Guide to set up the new PTR/TRAP 5.x primary and secondary nodes as a cluster. At this point, both nodes have data fully synchronized between them and they are ready to provide High Availability as a cluster.
Upgrading From 5.x to Newer Versions¶
If you have already upgraded to a 5.x-related version, and you wish to upgrade to a newer version of the application, follow the instructions in the Threat Response Console Guide (New) and scroll down to the Upgrade subsection.
Upgrading Between 5.x Versions on AWS¶
Please refer to Upgrading Threat Response on AWS in the AWS Installation Guide for information on how to upgrade a PTR/TRAP instance that runs on AWS.
FAQ¶
Upgrade Requirements¶
Why must you set up a new virtual appliance when you upgrade to PTR/TRAP 5.x?
Due to the proprietary nature of the platform applicable to older versions of PTR/TRAP, it is not possible to perform major “in-place” updates to the virtual appliance. Since PTR/TRAP 5.x includes a major update to the underlying platform and a departure from the old system, it is necessary to set up a new virtual appliance for 5.x and to migrate the preexisting data (from the old instance).
Which older versions of PTR/TRAP can be upgraded to 5.x?
Any older version of PTR/TRAP can be upgraded to 5.x by following the steps described in the sections above.
How long does it take to upgrade to PTR/TRAP 5.x?
Apart from the time that it takes to generate the backup on the old PTR/TRAP instance and to install the new virtual machine, restoring data on the PTR/TRAP 5.x instance takes about the same amount of time as “in-place” upgrades on previous versions of the product. Note that the amount of time depends on the size of the data (backed up and restored), which is a function of the volume of alerts and incidents stored in the system.
Upgrading¶
Since upgrading to PTR/TRAP 5.x requires setting up a new VM, can it use the same IP address and hostname as an older instance?
Depending on the network topology and deployment environment of the old and new PTR/TRAP instances, it may or may not be possible to reuse the same IP address and hostname. For example, in a DHCP-only network, the new PTR/TRAP instance obtains a different IP address automatically. Such a case also requires a separate hostname.
In case the same IP address and hostname need to be retained, the older PTR/TRAP instance must be fully powered down to avoid network errors.
In the event that the new PTR/TRAP instance is set up with a different IP address and hostname, the firewall and proxy rules in the network must be updated to enable the new PTR/TRAP instance to communicate with external applications, such as Overcast, Exchange, LDAP, and TAP (and any other alert sources and enrichment applications).
Why should the “Validate Encryption” option be checked when restoring a backup?
Keeping the Validate Encryption option checked ensures that the system validates the master secret applied from the older version of PTR/TRAP (where the backup was taken). If the master secret does not match, the “restore” operation does not proceed further. Note that if this option is turned off, or unchecked, the “restore” operation completes, but the data is in an inconsistent state.
Should the “Restore admin password” option be turned on when restoring a backup?
The Restore admin password option applies the password of the system-defined admin user account on the old PTR/TRAP appliance to the admin user account on the PTR/TRAP 5.x appliance. It does not affect any other administrative user accounts defined in PTR/TRAP.
Validating a License¶
What is Overcast?
Overcast (https://overcast.proofpoint.com/) is the name of the Proofpoint-owned cloud service used by Threat Response/TRAP to validate licenses, calculate certain alert metrics, and proxy connections to shared services.
Why do licenses need to be validated following an upgrade to PTR/TRAP 5.x?
PTR/TRAP 5.x includes an updated process to provision licenses for the application. This process enables Proofpoint to request, provision, and manage licenses across different products. In the long run, this benefits our customers. As part of the updated process, Proofpoint validates older licenses and flags their usage for tracking and management purposes and therefore, (as a one-time step), customers are asked to validate their licenses on an upgraded instance of PTR/TRAP 5.x.
Why does PTR/TRAP 5.x require connectivity to Overcast at the time of license validation?
PTR/TRAP 5.x must have connectivity to Overcast in lieu of the need to validate licenses after an upgrade. This can be set up either with the networking configuration of the VM or via proxy server on the Licensing page. An HTTPS request to this URL is used by the system to validate any license keys migrated from an older version.
Note
Connectivity to Overcast is also required when PTR/TRAP 5.x is deployed for the first time and a newly issued license key needs to be put into the system.
Can connectivity to Overcast be set up via proxy server?
The Licensing page enables the configuration of a proxy server with a hostname or an IP address and a port for cases where HTTPS communication between PTR/TRAP 5.x and Overcast must be directed via proxy server. This page also provides an option for basic authentication with this proxy server via username and password.
Note
The proxy server configured here is only to be used to validate the license on the PTR/TRAP instance with Overcast. It is not to be used for any other network communication (into or outside of the appliance).