About Threat Response Auto-Pull (TRAP)¶
What is TRAP?¶
Threat Response Auto Pull is a licensing agreement for Threat Response that allows customers to ONLY leverage the email quarantine functionality. Threat Response Auto-Pull automates quarantine of messages containing threats (URL or attachment) across Exchange (2010, 2013, 2016), Office 365, Google G Suite Gmail App and IBM Domino. To learn more about full Threat Response functionality, please, refer to the following document Threat Response (PTR).
While Proofpoint’s Email Protection block rates (99.9%) are the best in the industry, in some cases threats are delivered to users, and that might happen for the following reasons:
- URLs are pointers to content and content can change post delivery
- Attachments sometime include URLs which point to dynamic content
- No system is perfect. Unlike other vendors, we don’t claim we block 100%
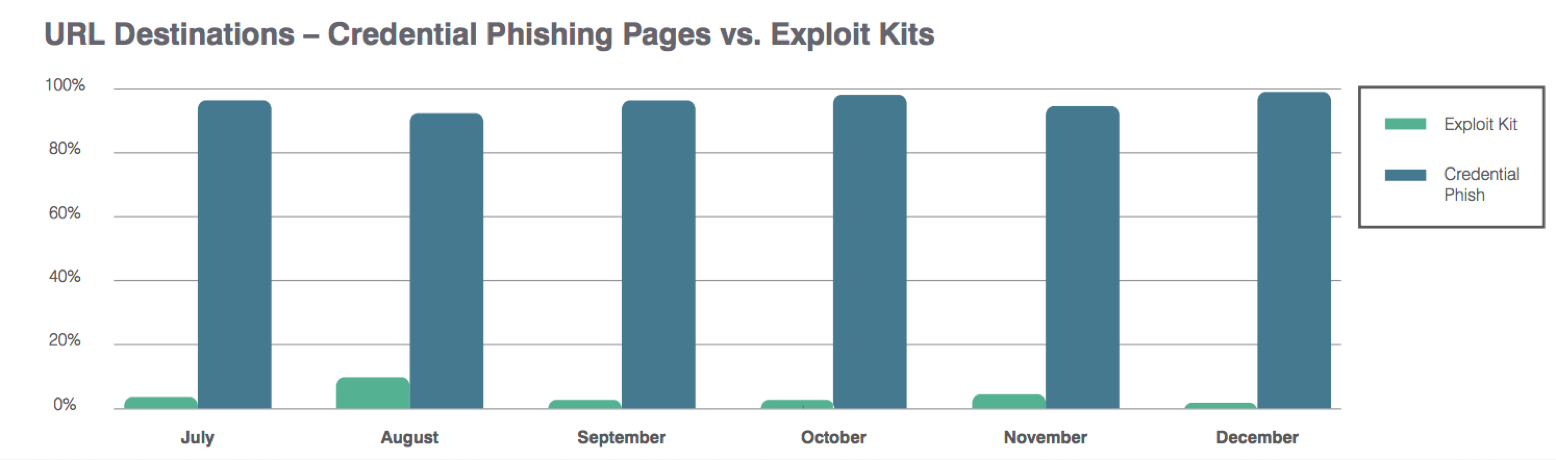
The bar chart below shows how during 2016 attackers are migrating their techniques by using more credential phishing pages as opposed to websites and URLs that serve exploit kits.
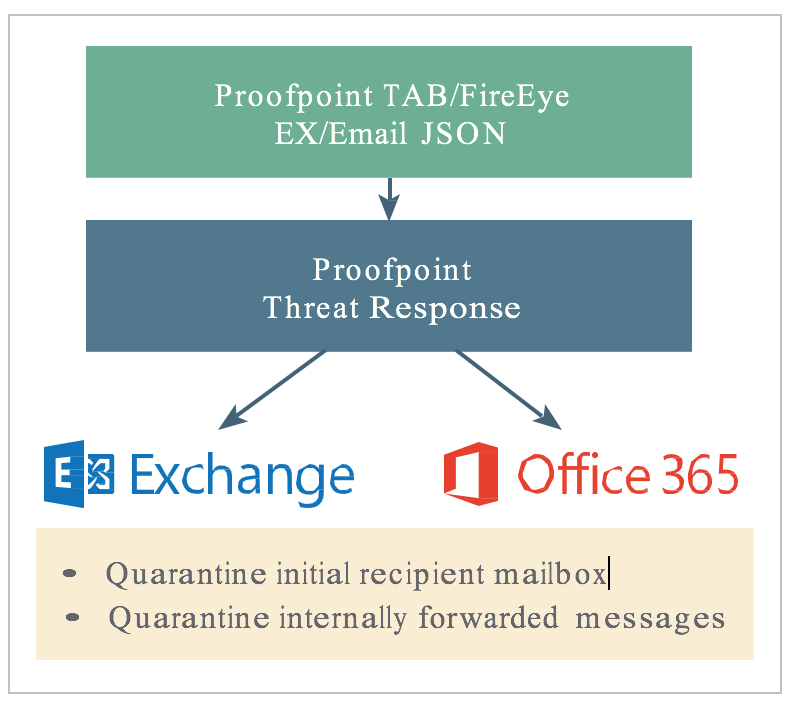
Threat Response Auto-Pull is an entry level version of Threat Response that delivers the Email Quarantine function when connected to Proofpoint Targeted Attack Protection (TAP) and on-premise Exchange, Office 365 or Google G Suite Gmail App. TR Auto-Pull also accepts FireEye EX and JSON alerts.
The use case is simple: when malicious email is detected, detecting systems send an alert to Threat Response with information about the message. Threat Response then goes into Exchange, O365, or Gmail to move the message into quarantine. Auto-Pull will also then look for forwarded copies of the message in other mailboxes on the same server and move those to quarantine as well.
Threat Response Auto-Pull includes adapters to connect Exchange, O365, TAP, FireEye EX, and JSON sources in minutes, so no additional systems or connectors need to be purchased. Admins only need the appropriate credentials, for Exchange and O365 for email retraction.
TRAP workflow overview¶
Email protection systems process thousands to millions of messages a day. Even with the most effective solution, such as Proofpoint’s protection and sandboxing platforms, there will always be some messages that make it through to a user’s inbox. If we’re able to block 99.9% of the malicious messages sent to the enterprise we still need to address the 10s to 100s of messages that are able to make it through. Proofpoint’s Threat Response platform can help mitigate the potential impact of these messages through it’s TRAP (Threat Response - Auto Pull) feature.
Let’s look at Threat Response Auto Pull workflow.
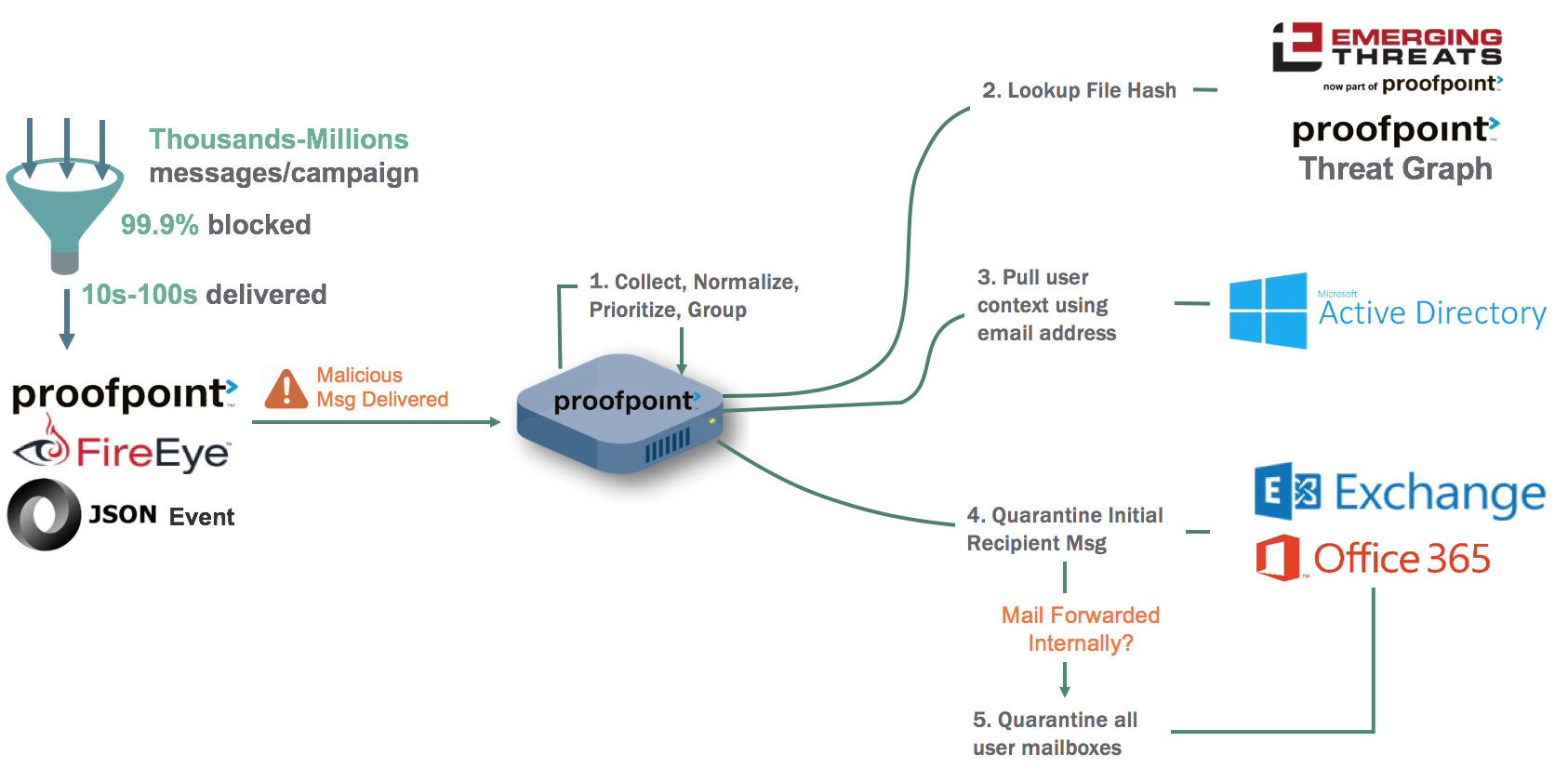
A platform such as Proofpoint’s Targeted Attack Protection (TAP), FireEye’s EX, or even a custom JSON source can be used to provide TRAP with alerts about the messages that have been delivered to mailboxes in the mail environment.
Once TRAP has received the security alert it will take the following actions:
- TRAP will collect the alerts, normalize the information, and prioritize the alerts by assigning a threat score and grouping similar messages by recipient and known malware campaigns.
- TRAP will take the IP/Host names, URLs and MD5 hashes that are sent in a forensics report from the alert sources, search reputation and intelligence repositories and identify if any of these repositories contain related threat intelligence information.
- TRAP can connect to Active Directory via an LDAP call and collect information about the user associated with the email address. The LDAP attributes that are collected provide insight into who’s being targeted/impacted by email attacks.
- TRAP will relocate the identified message(s) from the recipients and place them in a quarantine mailbox where they can be reviewed and examined but where the end user can’t access them.
- Once the message is located TRAP can identify if the message was forwarded to someone else. If it was, then TRAP can search associated mailboxes for the forwarded messages. If those messages are located they will be quarantined as well. TRAP will continue to take these tracking actions until all copies within the environment have been quarantined.